YellowKey Tool Bypasses Windows 11 BitLocker Using Only a USB Stick
Nightmare-Eclipse, a cybersecurity researcher previously known for a controversial reveal of three Windows Defender zero-day exploits seemingly rejected by Microsoft for petty reasons, has followed up with information regarding a BitLocker bypass vulnerability dubbed "YellowKey." Nightmare-Eclipse describes the vulnerability as one of the most insane discoveries ever, even stating that it "almost feels like a backdoor."
Nightmare-Eclipse considers this a backdoor because the bug isn't present anywhere except within the WinRE (recovery environment) and that the same component is present in Windows but without the functionality needed to bypass BitLocker. Additionally, only Windows 11, Windows Server 2022, and Windows Server 2025 are affected, not Windows 10. In order to exploit the vulnerability, one need only copy the FsTx folder to "System Volume Information\FsTx" on their recovery drive, boot into WinRE by holding Shift when restarting, and holding CTRL during the restart. This results in what we have pictured below: a shell with unrestricted access to the BitLocker-protected disk volume.
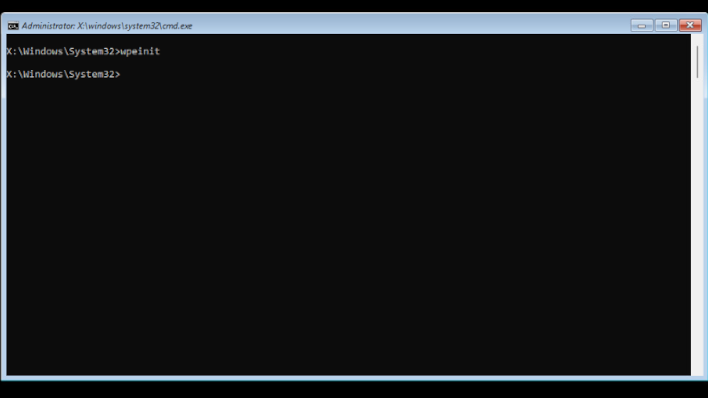
Image Credit: Nightmare-Eclipse on GitHub
In light of recent improvements to BitLocker, it's somewhat of a surprise to see just how easily it can be defeated without specialized tools. Perhaps the recent addition of hardware-acceleration introduced this vulnerability, since that functionality isn't available on Windows 10. It's hard to say at this point. While the GitHub disclosure claims it's a backdoor, coverage from other researchers like @KevTheHermit on X/Twitter emphasize the inconsistent nature of the exploit, which can require repeated attempts. It still works, but it would be odd for an intentional backdoor to function inconsistently.
In addition to YellowKey, Nightmare-Eclipse has also disclosed GreenPlasma, a severe elevation of privilege vulnerability that allows attackers to gain full system-level control. Fortunately, that disclosure does not include the code needed to execute the exploit, but it does paint a concerning picture for Windows users hoping to keep their PCs secure. Hopefully Microsoft can patch these holes sooner rather than later, and perhaps mend a clearly-disastrous relationship with this incensed, and highly-motivated researcher.
Image Credit: JanBaby on Pixabay (header)


