Official CPU-Z And HWMonitor Installers Infected With Malware After Site Breach
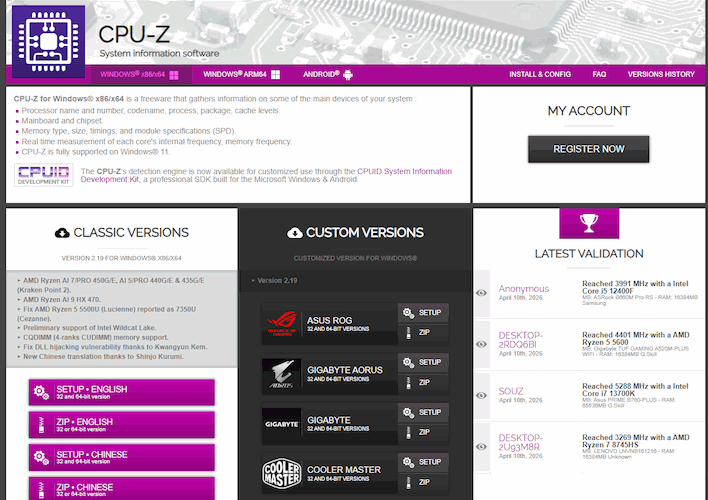
Rather than compromising the tools themselves, attackers targeted the delivery layer. The official download infrastructure was altered so that users requesting installers for CPU-Z and HWMonitor were served trojanized versions. The binaries appeared legitimate and were delivered through trusted channels, including links accessed via the apps themselves.
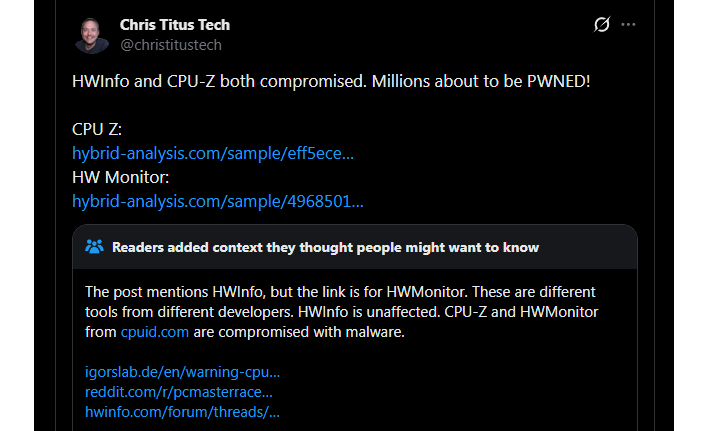
YouTuber and all-around tech guy Chris Titus was among the first to raise the alarm publicly, with confirmation soon after from vx-underground, which stated that the site was actively distributing malware during the window of compromise. According to further reporting and analysis, the attack window lasted roughly six hours before being shut down.
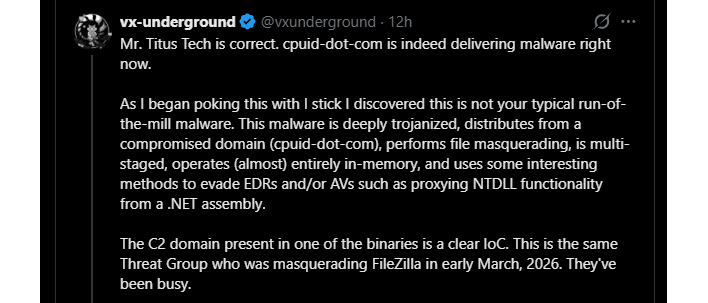
The malware experts at vx-underground immediately noticed that the payload is more sophisticated than your average smash-and-grab installer trojan. Once executed, it uses DLL sideloading (via a fake CRYPTBASE.dll) to blend into normal system behavior. From there, it loads additional code almost entirely in memory, making it harder for traditional antivirus tools to detect.
Key behaviors include a multi-stage loader with embedded shellcode, early callout to command-and-control infrastructure using DNS-over-HTTPS, use of PowerShell and system tools for follow-on payloads, persistence mechanisms involving MSBuild and script-based execution, and a primary goal of credential theft, especially browser-stored data. vx-underground described the malware as "not amateur work," noting its use of evasion techniques and staged execution.
This matters because it wasn't a case of "don't download sketchy software." Users did everything right; they went to the official site and downloaded what was supposed to be a safe app. Security researcher Mark Lynd summed it up cleanly: "The cpuid.com attack is the whole supply chain problem compressed into one incident [...] Trust the hash, not the domain." The attackers didn't break trust in the software; instead, they abused trust in the distribution channel.
As of now, the malicious downloads have been removed and the site is no longer serving infected installers. There's no indication the original software itself was backdoored or that CPUID's build environment was compromised. If you downloaded CPU-Z or HWMonitor during the affected window, assume that system was compromised, change any and all passwords that could have been stolen (particularly anything stored in your browser, enable MFA everywhere, and run security scans or even reinstall your OS if you want to be sure.