Microsoft Office Zero-Day Exploited Days After Emergency Patch, Update ASAP
In any case, it's remarkable to see how dangerous even an already-patched exploit can be in the hands of determined cybercriminals. It also shows the importance of keeping all software up-to-date for governments and agencies dealing with high-sensitivity information, since a major exploit can and will end up in those inboxes even if it's already been patched. Cyber criminals know that just because a patch exists doesn't mean that it has yet been applied, and for users who may not have the tech savviness or privilege to apply those updates as soon as they release, these circumstances become very dangerous very quickly.
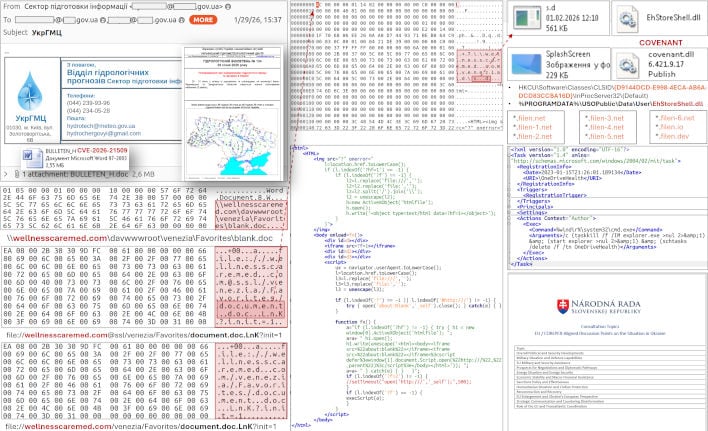
Hopefully, impacted users are able to clean their systems and apply the new update as soon as possible. The COVENANT malware installed by these attacks is commonly used in ransomware attacks thanks to its ability to provide persistent access to compromised systems, and its appearance on a government or enterprise network could prove truly disastrous. While common readers and users are unlikely to be targeted by such sophisticated attacks, being unguarded from them could still lead to a major loss in data, privacy, security, or even finances.
As highlighted by BleepingComputer in its coverage, this major CVE-2026-21509 exploit was still seen in the wild in the immediate days following the emergency update. Users must stay apprised for exploit news like this—even the best efforts of developers can see other links on the chain compromised, and ironing out a major malware operation still sees others emerge with similar or evolved tactics in due time.
Image Credit: CERT.Gov.UA