BeatBanker Malware Spoofs Starlink App To Take Over Android Devices
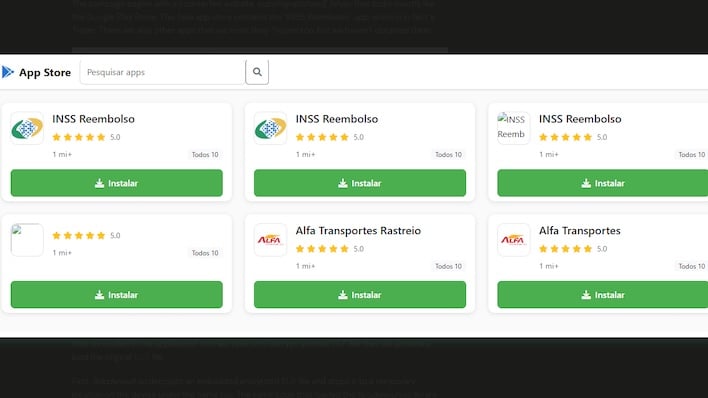
Users have been educated on the importance of sticking to official sources when downloading apps to their devices, and attackers are leveraging this to their advantage to spread BeatBanker. Targets are directed to a website that is a mirror image of the Google Play Store, which hosts apps that appear legitimate, such as Brazil’s Instituto Nacional do Seguro Social (INSS), which is the country’s social security portal.
Once installed, it takes advantage of granted accessibility permissions to display a web page that mimics cryptocurrency apps to steal funds from a user’s account. Moreover, it installs a cryptocurrency miner to commandeer device resources, although it starts and stops to get the most out of the device during opportune moments.
BeatBanker also goes to great lengths to remain undetected while achieving persistence on a device. It does this by playing “an almost inaudible audio file on a loop so it cannot be terminated.” Additionally, it keeps tabs on device statistics like battery temperature and percentage or if the device is currently in use to avoid detection.
However, the development of this malware and method of distribution has not remained static and limited to the Google Play Store lookalike. The researchers discovered a variant of BeatBanker being deployed through a fraudulent Star Link app, with this version having added functionality that includes a remote administration capability of infected devices.
Android users should continue to follow the advice of sticking to the official app store when downloading apps to avoid this kind of malware, but will need to be more vigilant by paying closer attention to whether the listed developer is legitimate. It’s also wise to check on permissions currently granted, particularly if they involve accessibility services.

