SolarWinds Russian Nobelium Hackers Strike Again, Compromise Constant Contact Reports Microsoft
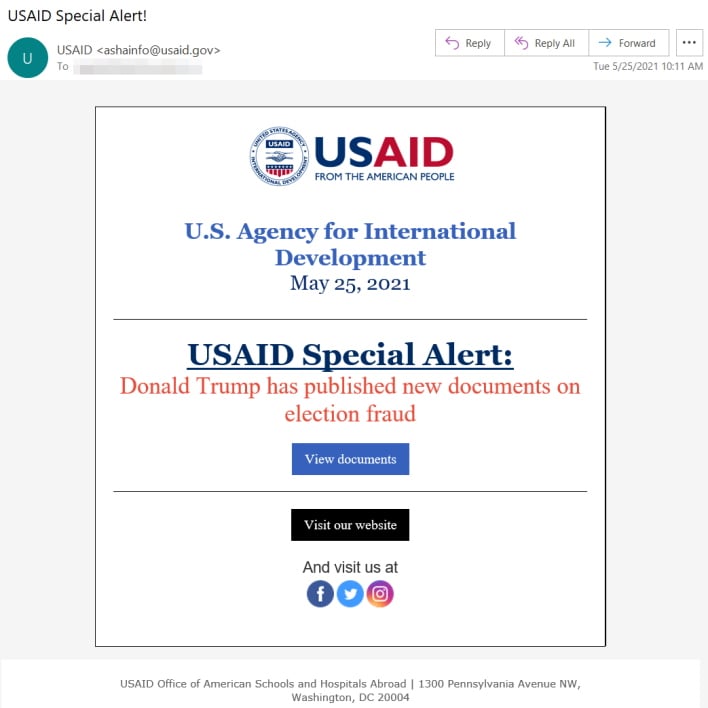
Yesterday, Microsoft reports that Nobelium started its attacks this week by breaching USAID's "Constant Contact" account, which is simply an email marketing account. Using this account, the threat actors were "able to distribute phishing emails that looked authentic but included a link that, when clicked, inserted a malicious file used to distribute a backdoor we call NativeZone." This malware could allow the hackers to steal data, infect other computers on the network, and more. However, Microsoft reported in a separate blog post that Nobelium had been phishing since early in January this year.
Furthermore, Nobelium has been targeting organizations that affect "issues of concern to the country from which they are operating." In this case, Nodeblium's targeting of human rights and humanitarian organizations shows a political motive to accomplish objectives. Also, these types of nation-state cyberattacks are not slowing in the slightest. There has been a massive uptick in threats, and yet rules for security in cyberspace are minimal and need to be expanded upon.
As always, Microsoft will continue to track Nobelium, and USAID has likely started an investigation to figure out how the initial breach happened. Hopefully, this attack and the recent Colonial Pipeline attack will spur better legislation and rules for cybersecurity. However, this is not the end of cyberattacks such as this, so stay tuned to HotHardware for updates.


