A New Menacing SharkBot Banking Trojan Lurks For Android Phones On Google Play
Discovered in October of 2021 by Cleafy, SharkBot is somewhat unique when compared to other bank stealing malware for Android, like TeaBot and others. The malware uses a few different methods of attack and data gathering, first and probably the easiest to catch is an injection or overlay. While the malware software is running in the background it can detect common banking or financial applications then overlay a fake login screen that looks legitimate to the user on top of the actual app, a rather effective way of stealing login data. Next, a simpler and somewhat classic approach is nothing more than simple keylogging, it detects user input and sends that input out to a server maintained by the malware host. This bot can also intercept SMS messages, so even if you have 2-factor or multi-factor authentication that relies on text messages, you can still be compromised. Lastly, it can take control of your device.
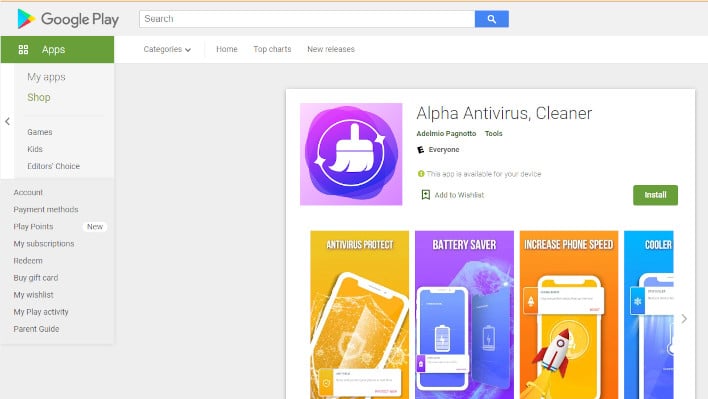
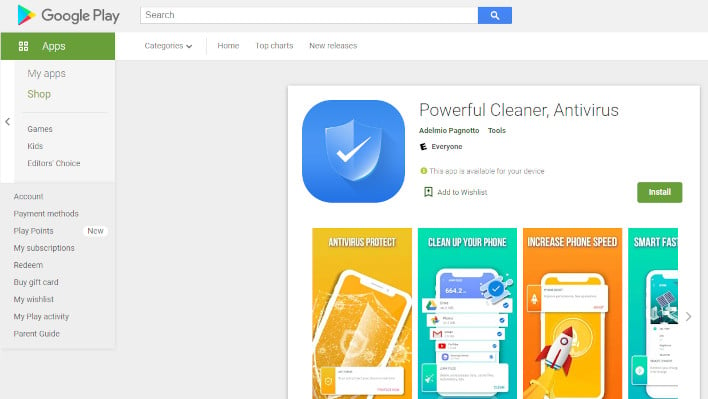
There are some things you can do to protect yourself, though. When it comes to software like anti-virus, always go through a trusted provider, even sometimes directly through a retailer or the originating website of the trusted anti-virus software itself. Double-check reviews on the play store, but be wary, some malware applications do have positive reviews because they actually do what is said 'on the tin', even though they still contain malware.
But what if you've already been infected? Well, first of all, we're sorry to hear that, and based on what most security researchers have discovered about SharkBot, your data has probably already been compromised. It is highly advisable that you change your passwords and login details, using a different device, and potentially change your passwords elsewhere, if you've the same credentials for other services. You will also need to uninstall the offending application and scan your device with an updated, trustworthy anti-malware tool and hope that it finds and removes SharkBot. Worst case scenario, assuming your personal files are backed up, resetting your phone may be an option.
- com.abbondioendrizzi.antivirus.supercleaner
- com.abbondioendrizzi.tools.supercleaner
- com.pagnotto28.sellsourcecode.alpha
- com.pagnotto28.sellsourcecode.supercleaner

