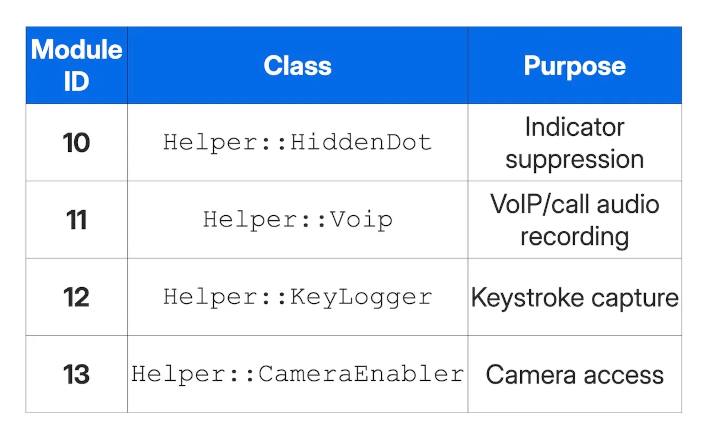
iOS users may already be aware of the commercial spyware dubbed Predator, but may not know exactly what it's capable. Fortunately, malware researchers Nir Avraham and Hu Ke have published a detailed write-up on how the Predator spyware works, including how "a single hook defeats both camera and microphone indicators simultaneously." The Predator spyware contains a helper module with 4 distinct other modules: HiddenDot, Voip, KeyLogger, and CameraEnabler. Working together, all four modules of Predator can enable full surveillance of a compromised iPhone without giving away any apparent "tells" to the end user that something is wrong. Since it's a much more thorough, extreme piece of malware versus
previous exploits, which were either limited in scale or required
direct physical access to a device, a breakdown like this is essential information for future patching efforts.
There's essentially a single hook that defeats all indicators simultaneously. Predator's code hook function is mounted inside iOS' SpringBoard system process and intercepts sensor activity updates from ever reaching the UI layer, so the indicators never appear. One exception to this is with VoIP recordings, where it has to rely on the HiddenDot module for stealth instead. CameraEnabler and VoIP modules hook into the mediaserverd system process as well, ensuring that nothing done on the phone escapes the eyes of the attacker while effectively turning iOS' own system processes against the end user.

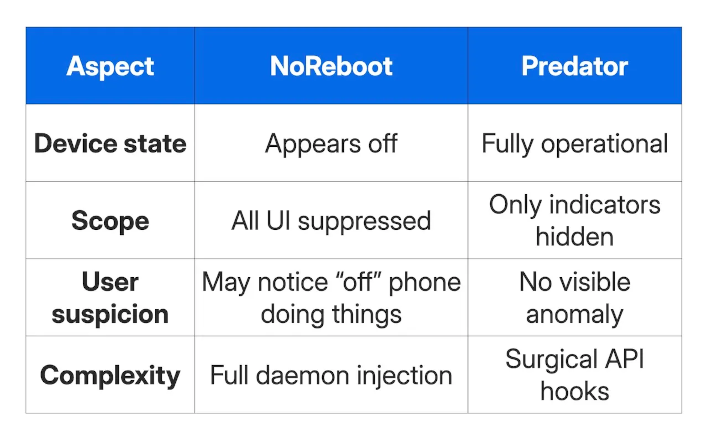
The research also highlights how Predator is distinguished from another major piece of iOS malware, called NoReboot. With NoReboot, the phone appears to be off while it's still being controlled by attackers. With Predator, only surveillance indicators are suppressed, giving the end user the impression that the device is working normally and no indication that they're being spied on. Predator is so stealthy that detection requires users to monitor system processes or identify key intervals at which the camera or mic are in use by scouring logs.
The full technical rundown on
Jamf.com details the code used to make these exploits possible, and will hopefully make it easier for Apple to identify and iron out vulnerabilities in future iOS updates. For now, all users can do is look out for red flags and make their iOS devices are fully updated.