A cyber risk and security analysis company by the name of Cyble has discovered that there are a number of websites distributing a version of
MSI Afterburner laced with various strains of malware. Those who accidentally download this widely popular graphics card utility via one of the cunningly crafted spoof domains could face
malware issues such as; unwanted
crypto mining software, and information stealing software.
MSI’s Afterburner is a very popular free utility for owners of
graphics cards, for owners of all brands (not just MSI) and architectures (AMD or Nvidia). However, enthusiasts looking to install Afterburner on a new PC, or grab an update via the web, should be extra careful where they get it. Cyble Research & Intelligence Labs (CRIL) have observed nearly 50 dodgy-domains come and go since early September, where MSI Afterburner is sneakily bundled with a selection of malware.
Specific malware apps that are being duped with a genuine version of MSI Afterburner include; XMR Miner, and Redline Stealer. CRIL provides some technical details of both malware installations. For news purposes it is sufficient to say that these malware apps are secretly installed alongside the genuine MSI Afterburner, without user prompting, from download files with innocuous names like browser_assistant.exe, install.exe, and comp.cab – distributed by the fake sites.
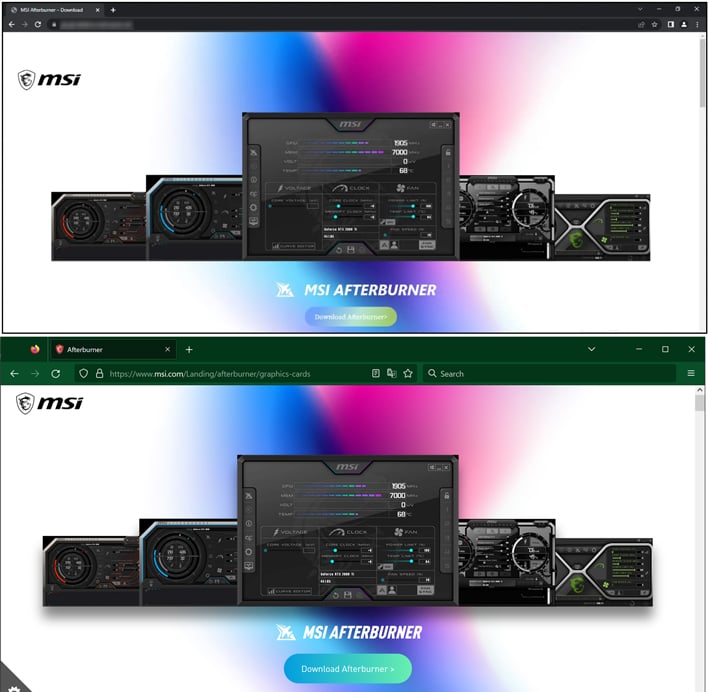
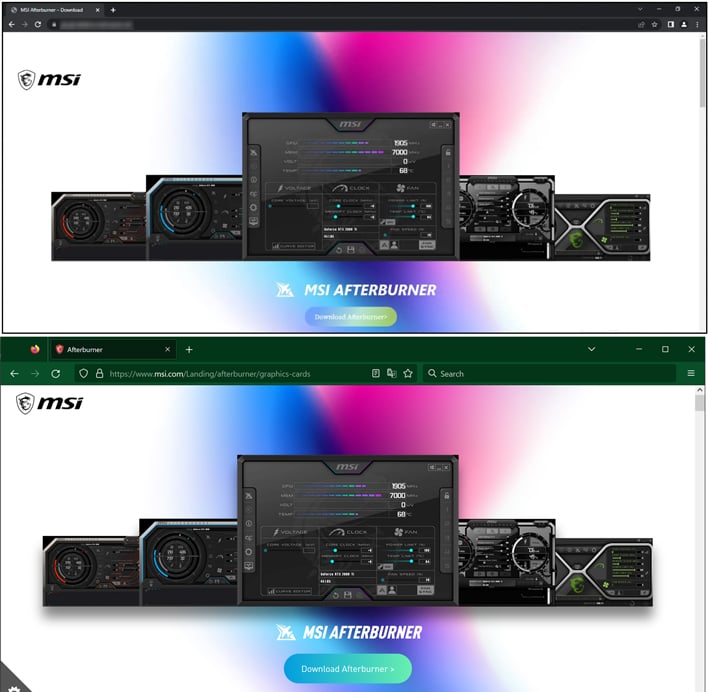
The non-official MSI afterburner sites setup by the threat actors (TAs) behind this malware campaign commonly contain text strings like msi-afterburner-download, and use less popular domain extension such as .tech, .online, and so on. We haven’t listed any particular overclocking-honey-trap site here, just in case a reader looking for an Afterburner download finds this article, then nonchalantly copies and pastes a malware site into the search/URL combo box of their browser. According to the source, the destination sites look very much like the official MSI site. Below, you can compare CRIL’s fake site screenshot to one we have just taken direct from the genuine
https://www.msi.com/Landing/afterburner/graphics-cards today.
Top (malware site) image via CRIL, lower image shows the genuine MSI site.
In a Google search for MSI Afterburner, none of the fake sites surfaced on our first page of results, and the top result was the genuine official link as reproduced in the above paragraph. However, some users on other platforms, in other regions, who perhaps don’t ‘Google’ things, might somehow opt to download from one of the non-genuine links with the malware infused download. Readers, please be careful out there, or some TAs might be able to steal your computer horsepower, or your personal information and passwords.