Glassworm Malware Campaign Uses Invisible Code To Infect Hundreds Of GitHub Repos
Per the coverage of Bleeping Computer and several research teams, GlassWorm targets cryptocurrency wallet data, credentials, access tokens, SSH keys, and developer environment data. With this information, GlassWorm can enable cryptocurrency extraction or other cyber attacks on the developers of infected code repositories. It's likely the largest-scale attack on independent software development efforts, skipping the usual vectors of browser extensions, ads, and commercial apps entirely to make the development environment unsafe for its users.
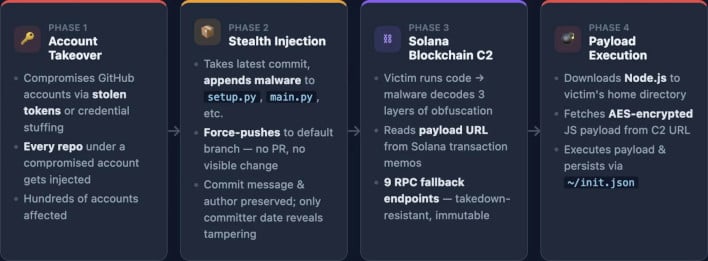
Image Credit: Step Security via BleepingComputer
Fortunately, GlassWorm can be detected, especially in the development environments it is now targeting. Developers are advised to search for suspicious i.js files in recently-cloned projects, review Git commit histories for anomalies, and inspect systems for the presence of the ~/init.json file that is used for persistence. Step Security in particular advises developers who install Python packages from GitHub or run closed repositories to search their codebase for the marker variable "lzcdrtfxyqiplpd", which is an indicator of GlassWorm malware.
As highlighted by the Bleeping Computer coverage, GlassWorm is not some immortal specter hovering over the development community, and can be defeated with enough education regarding its trademark tells and behaviors. But it does demonstrate that even independent developers, not just end users, are vulnerable to cyber attacks.
Image Credit: Bleeping Computer


