FBI Advisory Warns Active Hive Ransomware Gang Has Extorted $100M And Counting
Like most other ransomware gangs, Hive operates according to the ransomware-as-a-service (RaaS) model, with developers providing the group’s own proprietary ransomware to affiliates who carry out ransomware attacks. The developers then take a cut of the ransom payments made by victims. The Hive ransomware gang is particularly persistent when trying to collect ransom payments from uncooperative organizations. The advisory states that “Hive actors have been known to reinfect—with either Hive ransomware or another ransomware variant—the networks of victim organizations who have restored their network without making a ransom payment.”
The advisory also notes that Hive doesn’t use a single method of initial intrusion, as the gang’s various affiliate actors employ different tactics, techniques, and procedures (TTPs). Thus, organizations that have managed to address one or two vulnerabilities known to be leveraged by Hive affiliates may still be vulnerable to attacks by other affiliates. Hive affiliates have been found to use a wide variety of different techniques to gain unauthorized access to victims’ networks, often beginning with phishing emails that escalate to unauthorized Remote Desktop Protocol (RDP) or virtual private network (VPN) access. Some Hive affiliates have even leveraged critical security vulnerabilities to bypass multi-factor authentication (MFA).
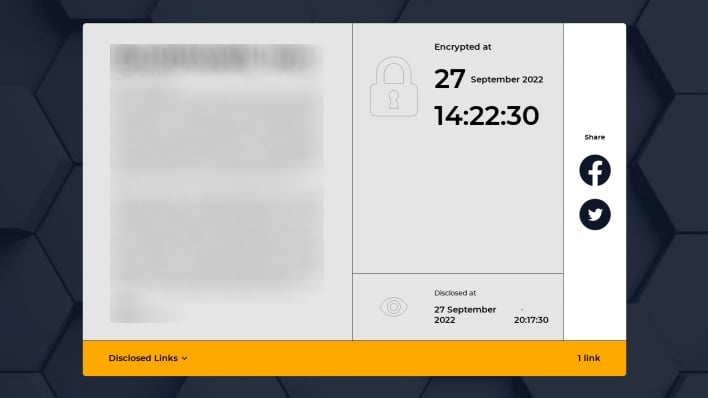
Hive also operates a site that exists specifically to facilitate communication between victims and the ransomware gang. Upon encrypting victims’ systems, the Hive ransomware leaves behind a ransom note that includes the .onion address for this site, as well as login credentials unique to each attack. The note instructs readers to use the Tor Browser to visit the site and enter negotiations with Hive’s “sales department.” The note also warns victims not to contact law enforcement or hire ransomware recovery services, stating that law enforcement won’t let victims pay to recover their files and that recovery companies usually fail in their negotiations.
The cybersecurity advisory recommends a number of measures that organizations can implement to reduce the risk of becoming the next Hive ransomware victim. These recommendations include applying security patches ASAP, implementing phishing-resistant MFA, maintaining offline encrypted backups, and monitoring logs for indicators of compromise (IOCs.) The advisory emphasizes the importance that healthcare and public health (HPH) organizations in particular implement such measures, given the sensitivity of the customer data stored in their systems.
| Vulnerability | Description |
| CVE-2020-12812 |
An improper authentication vulnerability in SSL VPN in FortiOS 6.4.0, 6.2.0 to 6.2.3, 6.0.9 and below |
| CVE-2021-31207 | Microsoft Exchange Server Security Feature Bypass Vulnerability |
| CVE-2021-34473 |
Microsoft Exchange Server Remote Code Execution Vulnerability |
| CVE-2021-34523 |
Microsoft Exchange Server Elevation of Privilege Vulnerability |

