StopCrypt Ransomware Evolved: Most Widespread Threat Now Avoids Detection
Earlier this week, researchers at SonicWall uncovered a new variant of StopCrypt, which utilizes “multi-stage shellcodes before launching a final payload that contains the file encryption code.” Breaking this down, at execution the malware loads a DLL file that is not used in the process. Then it drops into a time-delay loop with several iterations where the same data is copied repeatedly, suspected to be a detection avoidance mechanism. Following this, memory is allocated and modified using API function calls to set it to READ, WRITE, and EXECUTE.
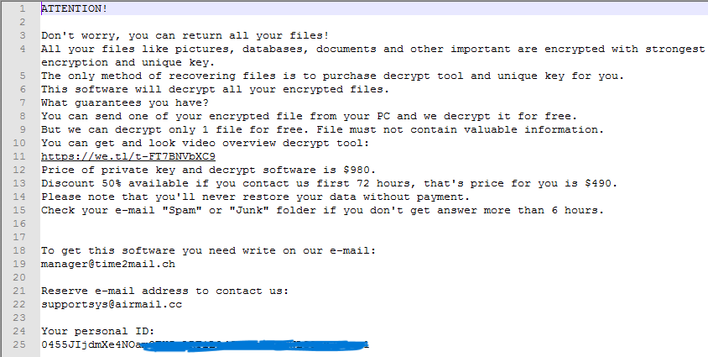
Afterward, the malware dynamically resolves APIs and constructs calls that eventually extract some information about the process and allocate some memory with the same READ, WRITE, and EXECUTE permissions. The second stage does process hollowing, whereby a legitimate executable has code removed and replaced. The third and final stage launches the hollowed process, copying the malware binary into a directory and adjusting permissions so that it cannot be deleted. The ransomware also creates a scheduled task that runs the final payload every five minutes, at which point your files are encrypted and have the .msjd extension added to them. Further, a ransom note is added to every encrypted folder where the demand for payment and contact info is laid out.
This is a concerning piece of malware, as indicated by the research, but we hope that security products like SonicWall's and Microsoft's Defender will detect and nuke it. Further, Windows now has built-in ransomware protection that may help prevent attacks like this. That's all fine and well for users who keep up with updates, but if this advancement is any indication, clearly enough people are vulnerable that StopCrypt is still lucrative for the threat actors to run and update.


