PasswordState Password Manager Leaks Enterprise Customer Credentials In Embarrassing Facepalm
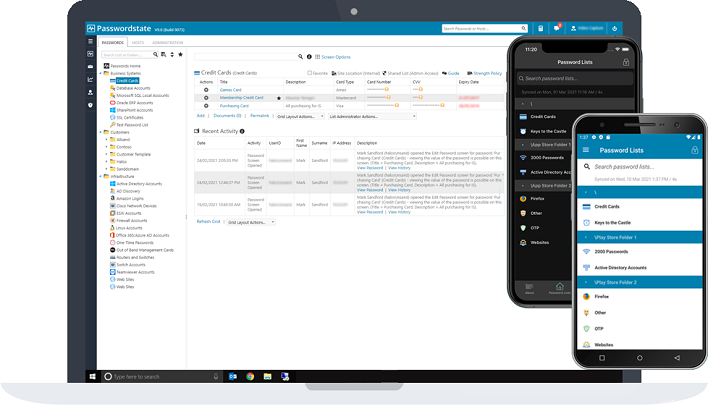
PasswordState is a self-hosted, as opposed to cloud-hosted, password management solution that integrates with Active Directory and handles a host of enterprise-related duties including auditing and its own API. Unfortunately, some of its customers who installed an update between 4:33 PM Eastern on April 20 and 7 PM Eastern on April 21 received malware as part of the upgrade process. This malware then uploads password data, running process information, system configurations, and much more to a third-party network once per day.
Click Studios says that a bad actor compromised the in-place updater on its own servers, so that when customers downloaded it, they would get the password-stealing payload as part of the update. Normally, the updater downloads additional files from a content delivery network (CDN) and performs the install. The infected updater grabbed extra data from another CDN, which then steals user credentials. The company has posted a hotfix that it urges all customers who installed the bad update to use, as it should remove the malware and restore security. To speed up the availability of a fix, the update is distributed as an archive and involves manually replacing infected files.
In total, Click Studio issued a statement which says the infected update was available for approximately 28 hours and then pulled and replaced with the previous version of the application. Because of the small window of opportunity, Click Studio says the number of affected customers is expected to be very small. The company has identified and contacted the customers it believes were affected based on their own CDN server logs, based on tracking who downloaded the bad update. However, the company says the number of affected customers may increase as more information becomes available.


