Self-Replicating P2PInfect Worm Is Leaving A Trail Of Malware In Windows And Linux PCs
The P2PInfect worm works by attempting to exploit CVE-2022-0543, a CVSS 10.0 critical vulnerability that allows for a Lua sandbox escape which could lead to remote code execution. Though this vulnerability is a year old, the researchers explain the scope of the issue is still unknown. This worm has also been observed infecting Redis servers on both Linux and Windows operating systems, making it “more scalable and potent than other worms.”
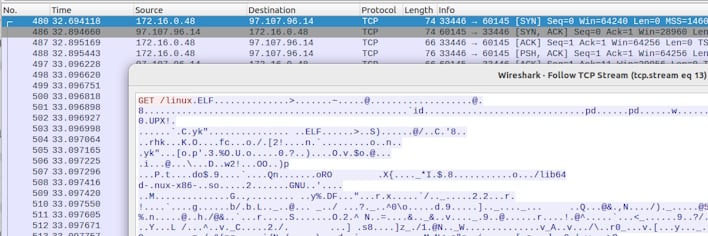
After exploitation of CVE-2022-0543 to gain initial access, it deploys a payload to establish communication with a P2P network. Once this communication channel is established, which acts as a command and control (C2) botnet network as well, malicious binaries and scripts are pulled down to do some enumeration of the host. It is thought that this is only the first stage of a larger attack, with instances of the word “miner” in the P2PInfect binaries. Though there is no clear indication that cryptomining operations occurred, it is still entirely possible among other features of the malware, such as “Auto-updating,” that would allow for new payloads to be pushed to the P2P network.
Interestingly, this campaign has not been tied to any groups that are known for targeting Redis instances or doing worm-like operations. Therefore, this may be an entirely new threat actor or otherwise malicious hacking group emerging. The researchers also note that this malware is “well designed with several modern development choices,” including the use of the Rust programming language allowing for “resilient capabilities and the flexibility to allow the worm to rapidly spread across multiple operating systems.”
To prevent this attack from affecting your Redis instance, you should ensure that Redis is updated to the latest version, or, at the very least, newer than redis/5:6.0.16-1+deb11u2, redis/5:5.0.14-1+deb10u2, redis/5:6.0.16-2 and redis/5:7.0~rc2-2.


