Microsoft Security Research Details SolarWinds Solorigate Elaborate Second Stage Backdoor Attack
Once on a network through the Solorigate backdoor (SUNBURST), getting anything done requires new malicious software and a level of secrecy that can be difficult to maintain. Moreover, when executing an attack, you do not want to burn the entire bridge if discovered on a network. Thus, the SolarWinds hackers attempted to separate their backdoor and the tools they used to collect and send data. You can see the extreme separation in the chart Microsoft created below.
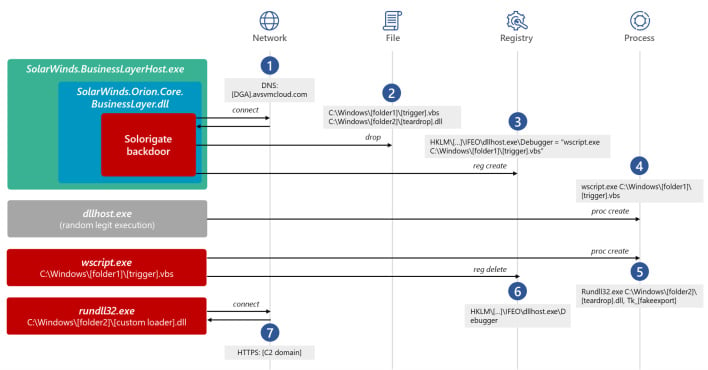
In total, as Microsoft explains, "As we continue to gain deeper understanding of the Solorigate attack, we get a clearer picture of the skill level of the attackers and the extent of planning they put into pulling off one of the most sophisticated attacks in recent history." The sheer level of complexity, planning, and execution make for an impressively concerning attack. However, this is not kudos to the hackers but a security warning to companies and organizations at risk. Furthermore, Microsoft's information can be crucial for stopping attacks like this in their future tracks.


