Looney Tunables Exploit Gives Hackers Root Access To Linux, That's All Folks
Glibc is the GNU C Library project, and it “provides the core libraries for the GNU system and GNU/Linux systems, as well as many other systems that use Linux as the kernel.” Effectively, any operation you do on a Linux kernel system has ties to this library in some form or fashion. Within this is a dynamic loader, which helps to prep and run programs on the system to see what shared libraries are needed by that program. With this, an environment variable called GLIBC_TUNABLES allows users to change library behavior on the fly to avoid requiring a recompile.
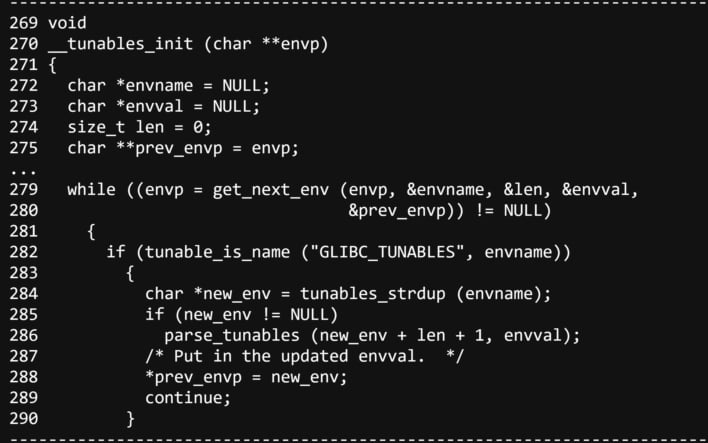
On the inside of glibc, a buffer overflow vulnerability was discovered in the function that handles GLIBC_TUNABLES. With exploitation, this would allow for full root privilege to be granted to a local attacker “on the default installations of Fedora 37 and 38, Ubuntu 22.04 and 23.04, and Debian 12 and 13,” likely alongside other distributions of the Linux kernel. The researchers at Qualys note that the issue was introduced in April 2021 with glibc version 2.34, which has since been updated four times.
Thankfully, this vulnerability and associated exploit was sent to RedHat early last month, was patched around September 19th, and had a coordinated release date yesterday. Further, as it stands, exploit code is being withheld, but it would not be outside the realm of possibility that another research team or threat actor develops an exploit to integrate into a kill chain. As such, it is recommended that system administrators patch their boxes against this threat to “ensure system integrity and security.”


