Hackers Are Exploiting This Microsoft Outlook Privilege Escalation Security Flaw
The vulnerability lies in a feature of Microsoft Outlook which allows a custom sound file to be loaded for notifications. Specifically, the sound file does not have to be local on the machine but can reside on a remote file share accessible via a Universal Naming Convention (UNC) path.
An attacker can craft a special email, typically containing a malicious calendar or meeting invite, which also forces the victim's computer to load a remotely hosted notification sound from an SMB share the attacker controls. The victim's computer automatically tries to authenticate via New Technology LAN Manager (NTLM), exposing hashed credentials to attacker. The attacker can then either attempt to recover the credentials via cracking, or else use them in a replay attack to authenticate with other services.
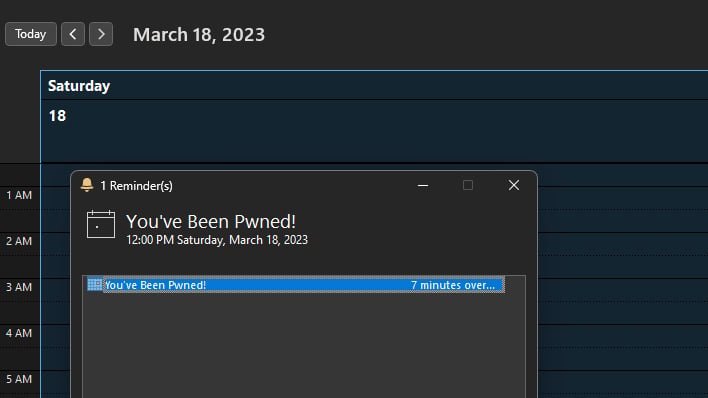
Critically, this process requires no interaction from the victim. Outlook automatically initiates the compromised remote file share as soon as the malicious message arrives in the victim's inbox.
To mitigate this, users or system administrators will need to install the necessary Microsoft Outlook security update or restrict NTLM's use for authentication. Further, organizations could also block outbound SMB traffic over port 445. This prevents the remote file sharing authentication attempt from occurring over the Internet. Microsoft has also released an audit tool on GitHub to see if your organization has been affected.
TrustedSec reports that Russian military intelligence has exploited this vulnerability for about a year, so patch now to stay secure.


