Mobile processor designer Arm has issued a security bulletin for developers using its Mali GPU drivers. The firm has warned that a flaw tracked as CVE-2023-4211 “may be under limited, targeted exploitation.” Affected devices include the
Google Pixel 7, Samsung Galaxy S20 and S21, the ASUS ROG Phone 6 and many more by firms like Oppo, Xiaomi, RealMe and Honor. GPU kernel drivers are now ready to patch most of the affected GPUs.
Arm Mali GPUs are very widely used in a diverse range of smart and computing devices like smartphones, tablets,
Chromebooks, and Linux machines. Several generations of affected GPU architectures span platforms where security updates aren’t likely to be forthcoming, like for older smartphones.
In its description of the flaw, Arm says that “A local non-privileged user can make improper GPU memory processing operations to gain access to already freed memory.” This method of access to system memory is a commonly exploited mechanism for
malware. A malicious actor could potentially use this opportunity to execute nefarious code or exploit other vulnerabilities.
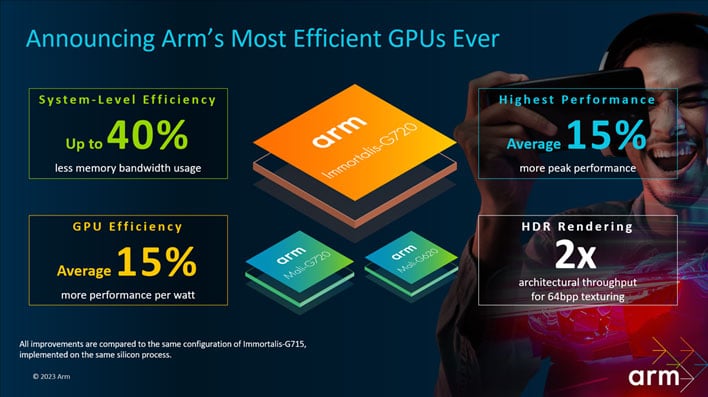
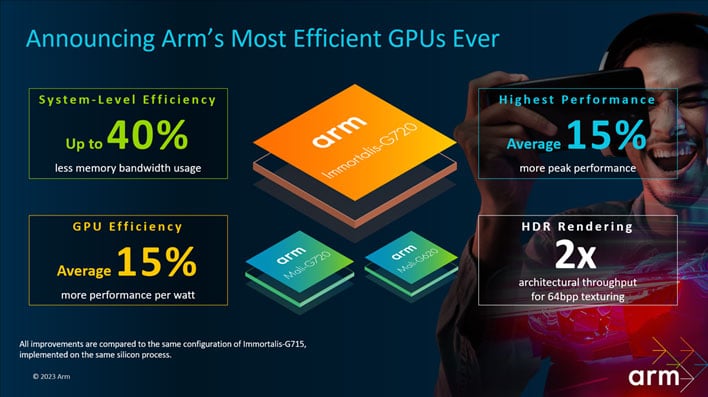
Arm has patched the CVE-2023-4211 flaw in its r43p0 kernel drivers for Bifrost, Valhall and Arm 5th Gen GPUs. As hinted at above, users of older devices will be lucky if they get updates to cover the CVE-2023-4211 flaw. Mali Midgard, Bifrost, and
Valhall GPU architectures were introduced between 2013 and 2019, and some Android vendors will only offer system and security updates for a couple of years. Users of Arm’s 5th gen GPU architecture will probably have the best luck, as it is pretty new, debuting in devices this summer. Meanwhile, developers using the Midgard GPU kernel driver are being asked to contact
Arm support.

Some relief for older device users may come from Arm’s statement that local device access is required to exploit the CVE-2023-4211 flaw. Attackers typically try to get this level of access by tricking users to download specially modified apps from outside the Google Play Store or Amazon App Store. Therefore, users of older devices which haven’t seen updates for some time would be wise to stick to the major official software repositories and reputable, well-known apps.
Arm also disclosed the CVE-2023-33200 and CVE-2023-34970 vulnerabilities in its
security bulletin on Monday.