Google Researcher Discovers Data-Snooping Downfall Flaw Affecting These Intel CPUs
So the more recent Rocket Lake, Alder Lake, and Raptor Lake processors aren't affected, but there's still a whole bunch of Skylake cores out there in the wild. Those chips are vulnerable to a hardware security flaw that has been titled "Downfall" by the person who discovered it, one Daniel Moghimi. He's a senior security researcher for Google, and he's devised two different ways to make use of Downfall.
In essence, the flaw itself comes down to the way the gather instructions are implemented in these CPUs. Like most Intel processors since the original "Core i" chips in 2008, Skylake cores are typically configured with simultaneous multi-threading, which Intel calls Hyper-Threading. Moghimi figured out that the AVX2 gather instructions—used for conditionally loading multiple floating-point values simultaneously—use "a temporal buffer shared across sibling CPU threads."
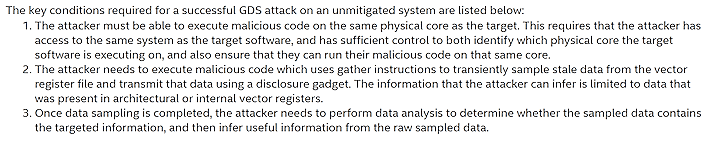
Moghimi figured out that, due to the way the processors transiently forward data to later instructions from this temporal buffer, it's possible for an application running on one logical core to leak information to an application running on the other logical core. This is obviously very bad, because it means that applications running on the same physical CPU could leak cryptographic keys and other sensitive data even out of a virtual machine or other sandbox, which happens to be the subject of the researcher's proof-of-concept.
If you're still concerned about the flaw, it's been mitigated in the latest Intel CPU microcode. Intel worked around the issue by preventing transient data forwarding after a gather instruction, however, the company notes that this could slash performance by half in "certain vectorization-heavy workloads." As a result, and owing to the relatively-mild severity of the flaw given the difficulty of deploying it, Intel says it has "an opt-out mechanism" in the microcode that allows the mitigation to be disabled.
Of course, you also could replace all your systems sporting Skylake CPUs with newer hardware that isn't affected by Downfall. That's probably what Intel would prefer, but it might not be a bad idea anyway. Even if you think your current system is plenty fast, Intel's newer chips have rapidly increased single-threaded performance due to stiff competition from longtime rival AMD, and they're also radically more power-efficient even despite high power usage under a full load. If a system upgrade is on the table, don't forget to check out some benchmarks to see if you're better off sticking with Intel or going red for your workloads.