Hackers Are Using NASA's James Webb Telescope Images To Disguise Malware Payloads
Like other pieces of sophisticated malware, the so-called GO#WEBBFUSCATOR campaign doesn't rely on getting someone to run a naked executable file. According to security firm Securonix, infections begin as a phishing email. The messages contain a Microsoft Word attachment called "Geos-Rates.docx," which downloads a malicious template file if opened. If Office has macros enabled, the application will execute a VB script in the template -- this is where the attack really begins.
The Go-based malware downloads what appears to be an image file named OxB36F8GEEC634.jpg. If you open it in an image viewer, you might not realize anything is amiss. The file appears to be a scaled-down version of galaxy cluster SMACS 0723, known colloquially as the Webb Deep Field. It covers a patch of sky about the apparent size of a grain of sand, but Webb's incredible optics and high sensitivity in the infrared spectrum reveals a sea of thousands of galaxies.
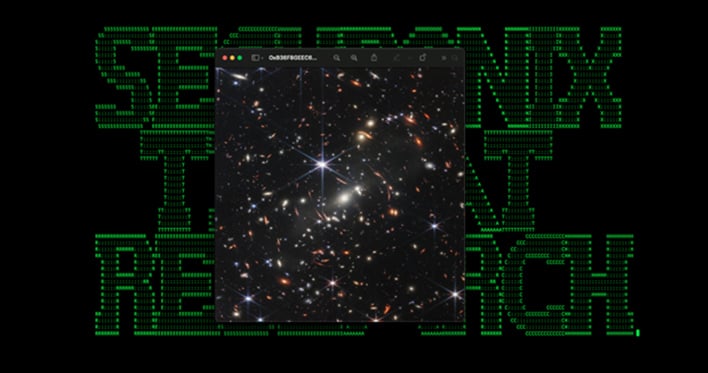
The victim of the malware, believing they have just gazed into the infinite, will go about their day not realizing that the image contained a Base64-encoded payload. The malware decodes that into an executable (msdllupdate.exe) and launches it. With the malware fully deployed, it copies itself to additional directories and adds registry keys to ensure persistence. Securonix reports that the malware grants the attacker remote control over the system. Researchers observed the authors using arbitrary enumeration commands, a common first step in analyzing a system for further exploitation.
You can avoid this nasty piece of code in a few simple ways, starting with this old chestnut: don't open files that arrive in suspicious emails, even if they aren't executables. You can also make sure macros are disabled in the Office suite as that's a common method of loading malware. Lastly, if you want to look at amazing images from the James Webb Space Telescope, just go straight to the source or let us highlight the most inspiring images for you here.


