iOS Devs Warn Apple Apps Ignore Privacy Settings And Track A Shocking Amount Of Data
Nonetheless, these new findings aren’t super surprising. In December 2020, Apple implemented its App Tracking Transparency (ATT) feature, which shines light on the data collection and sharing practices of apps in the App Store and gives users the option of disabling tracking and data sharing when it involves third-parties. However, while ATT can block apps from tracking users across third-party apps and websites, first-party in-app tracking is still fair game, meaning, Apple, among others, is free to collect user behavior data for its own purposes without violating ATT rules.
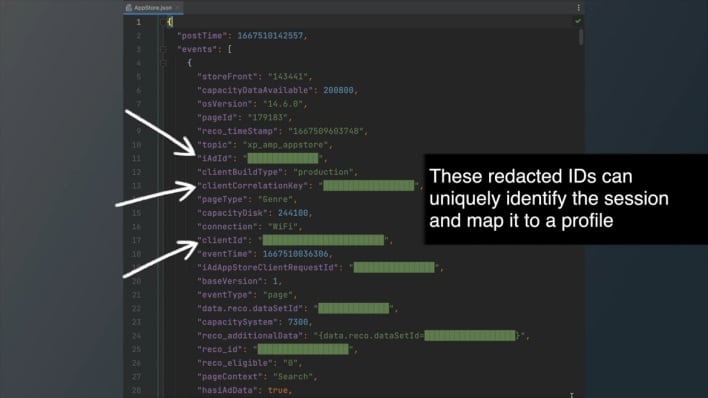
However, iOS developers Tommy Mysk and Talal Haj Bakry found that multiple Apple apps, including the App Store, the iTunes Store, Apple Music, Apple TV, Books, Stocks, send analytics data back to Apple regardless of whether analytics sharing is enabled or disabled in the Settings app. The developers made this discovery on an iPhone running iOS 14.6 that they had jailbroken, enabling them to decrypt requests sent to Apple and read the contents. Mysk and Bakry found that the requests contained multiple unique device identifiers, additional device information, and detailed user behavior information.
The developers analyzed outgoing network traffic on a non-jailbroken iPhone running iOS 16, the latest version of the operating system, and observed Apple apps sending similar requests to Apple. Without jailbreaking the phone, the developers can’t decrypt the requests and confirm that they contain the same user behavior data. Even so, the requests were sent with the same frequency and under the same circumstances as the ones observed on the jailbroken phone, which is good reason to believe that Apple apps on iOS 16 exhibit the same data collection behavior.
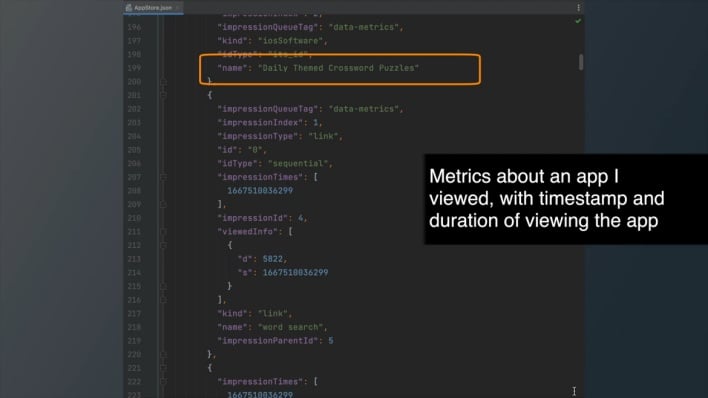
Regardless of whether the data collection and usage controls with the operating system and the apps themselves do anything, the developers are of the opinion that the amount of detailed information contained within the analytics data sent to Apple is “too much even if the user has consented to sharing analytics data with Apple.”