This Android Malware Silently Steals Your Credit Card Data Over NFC
The attackers have chosen to weaponize HandyPay, a legitimate NFC payment app that’s been available on the Google Play Store for several years, lacing it with code from an updated version of the NGate malware family. The infected app is distributed through a web page designed to mimic the official Play Store, with links being sent to potential victims using WhatsApp.
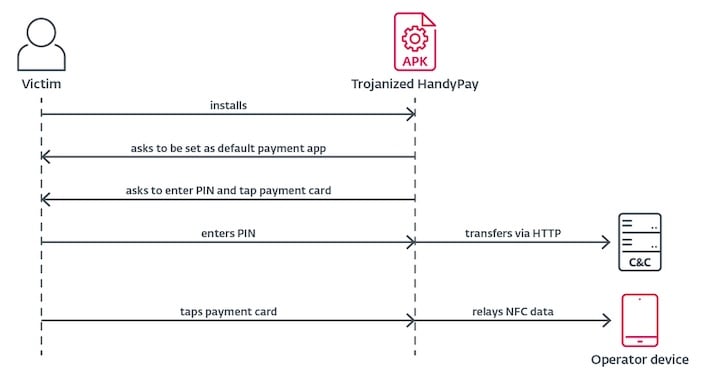
Once installed on a victim’s device the app operates the way a user would expect, however, in the background it collects and then sends payment data, including credit card numbers and security PINs, to a device the attacker controls. This information can then be used to perform contactless payments or even withdraw funds from a victim’s account.
The reason HandyPay was chosen is because it provides the capability for collecting NFC data for a mere 10€ a month, which is a drop in the bucket compared to the several hundreds of dollars other malware-as-a-service (MaaS) cost.
The security researchers strongly believe that generative AI was used in the creation of this compromised version of HandyPay. They share that “malware logs contain emoji typical of AI-generated text, suggesting that LLMs were involved in generating or modifying the code, although definitive proof remains elusive.”
The combination of AI generated code and the low cost of deploying this malicious app show how low the barrier of entry is for attackers these days. To avoid falling victim to this kind of malware, users are urged to stick to official app stores only.


