NSA Raises Alarm Over Chinese Hackers Hiding In Modified Cisco Router Firmware
The threat actor group, BlackTech, has been targeting government, industrial, technology, media, electronics, and telecommunications organizations worldwide, including military-industrial complex companies supporting both the US and Japan, since 2010. Per the joint alert, this group develops customized malware and tailored persistence mechanisms to compromise routers and maintain access to a victim’s network. Further, they have been known to use twelve or more custom malware families targeting Windows, Linux, and FreeBSD, some or all of which are updated regularly to evade detection by security tools.
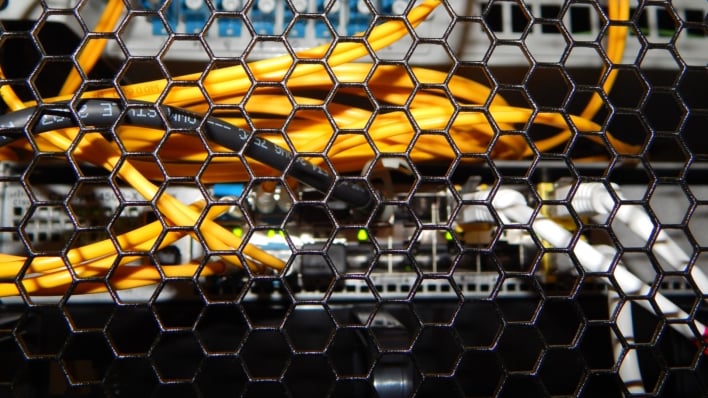
This group is also known to do what is called living off the land, where either preinstalled or common tools are used to execute the group’s actions while blending in with normal network and system activity. Once the group has compromised internal networks of international subsidiaries of US or Japanese companies, “BlackTech actors are able to pivot from the trusted internal routers to other subsidiaries of the companies and the headquarters’ networks.” This is done by gaining access and administrator privilege over network edge devices like routers and modifying the firmware to set up backdoors, gain access to the larger corporate network, and execute other activities. The advisory notes that while it is not limited to Cisco routers, the group has been observed "[replacing] the firmware for certain Cisco IOS®-based routers with malicious firmware."
To protect against BlackTech, the advisory recommends that organizations disable outbound connections, monitor inbound and outbound connections to any system, use network segmentation to isolate administrative devices, restrict administrative access to systems by IP address, and several other steps, which can be viewed here. CISA also recommends that organizations keep systems up to date with patches, disable unnecessary ports and protocols, replace EoL infrastructure, and implement a central patch management system.
At the end of the day, BlackTech is certainly not the only threat group able to lie low with advanced TTPs; they are just the only ones who got caught. As such, these cybersecurity recommendations are good even if you don’t think you would be a target of the group. You never know who or what might be lurking around your network or even just lying on the edges.


