Another day another
malware threat. Do you ever notice how, when you open an e-mail link, money in your bank account drains away? That shouldn't happen, but if it does, it's probably thanks to QBot's new distribution method.
You might be thinking, 'Hey, I'm smart enough to know I shouldn't click on iffy links!', but that doesn't mean the tactic doesn't work. Developers of malware have known this for years, and this is frequently a preferred method of delivery for malware. Well, distributors of a well-known banking trojan,
QBot, have decided to stop using one of its prolific distribution methods of "iffy Office attachments" and start sending people zip files with Windows Installers in them. Specifically MSI installers.
Microsoft did a study on the QBot malware in
December of 2021, pointing out that it is popular amongst malware distributors due to its modular nature. Saying that because of said modular nature, it allows distributors to pick and choose feature sets, which also allows them to modify them to make them harder to detect. Security researchers, though, believe that this move in distribution methods is related to Microsoft turning off VBscript in Microsoft Office
by default.
QBot, according to
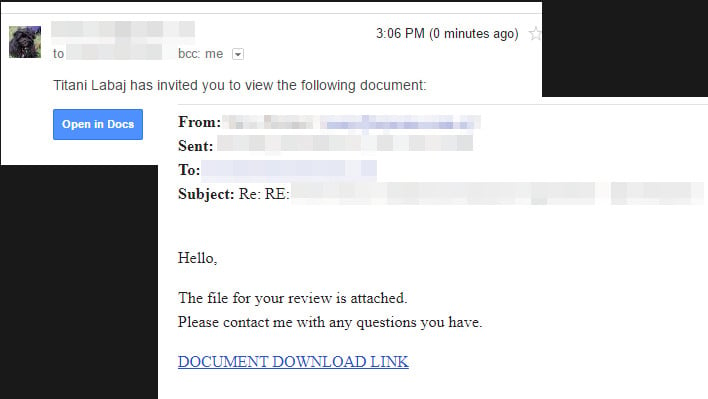
BleepingComputer, is most frequently used in efforts to affect large corporations. It is often the malware of choice for many ransomware groups as well, and because it can attack Active Directory admin accounts. It can also spread within networks. It is a particularly nasty piece of work. Some common methods of attack are also combined with what looks like legitimate e-mails from a spoofed version of a trusted contact. They can also look like a "secure file share", and they can even look like Google Drive, OneDrive, or DropBox file shares.

Best practices to protect yourself, and if you're a sysadmin your users, are to educate. Emphasize not clicking on links from unknown parties, always double-check the "from" field in your e-mail, and watch out for obvious typos and bad grammar. Of course, do not open attachments unless you're expecting one, and definitely do not open any files or installers that you do not know where the file originated from for certain. In most organizations, it is best to keep a policy to send out information about this on the regular.