Popular Password Vault Was Breachable By Bypassing Windows Hello Security Measures
Researchers from RedTeam Pentesting just put up a blog post regarding a vulnerability discovered in Bitwarden that would allow an attacker to steal your passwords with no user interaction required. While the problem was reported and fixed back in Bitwarden v2023.4.0 in April, it is still interesting to see the process behind this attack. With that, the story of breaking into Bitwarden begins with RedTeam Pentesting engaged in a penetration test of a client who had a Windows environment.

Though the team had already gotten administrative access to the domain controller, they wanted to see if they could access the backup server located off-domain. The hope was that they could find information or credentials that could lead to access to the backup server. While exploring, they found what appeared to be passwords stored using Bitwarden Desktop v2023.3.0 on workstations accessed through domain administrator accounts. With this access, the red team could have planted a key logger to nab the Bitwarden passwords and call it a day, but they did “not want to potentially disrupt the client’s business by using invasive techniques.”
With that in mind, they moved on to trying to crack the vault in more traditional ways, like a credential stuffing attack where previously compromised usernames and passwords were tried. These attempts proved unsuccessful, though. The team subsequently downloaded the main storage file of Bitwarden at %AppData%\Bitwarden\data.json, hoping they might find something interesting. What they discovered indicated that the Bitwarden vault could be opened using biometrics powered by Windows Hello, so the question became whether that was a viable attack vector.

To understand where the team is going, a little background about Bitwarden and how your passwords are protected in is order. The blog post explains that password vaults are not really protected with your master password, but rather with an intermediary account encryption key. This key is stored in the vault and is a derivation of the main password used in vault creation, which is also derived each time the password is entered to decrypt credentials. With biometric unlocks enabled, rather than storing the main password, the system can store an encrypted version of the derived key to use later. As such, acquiring the derived key is as good as having the vault password itself.
Following some digging and research, the team found a means by which the Windows Credentials API, which then used the Data Protection API (DPAPI), could be leveraged to grab the derived key. This worked by using the domain user password for the account. This meant that as long as a user password or a remote backup key stored on the domain controller was known, sensitive data could be decrypted, thereby bypassing Windows Hello and biometrics entirely.
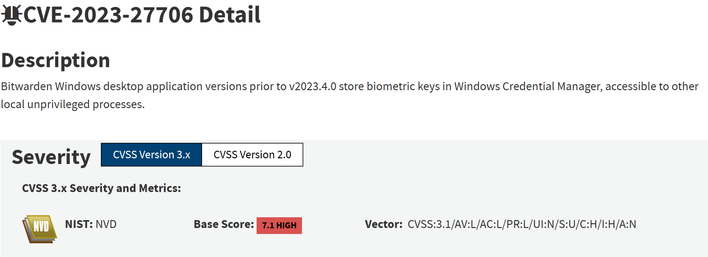
An excellent explanation and proof of concept is available here. Also note, this is not the first time this issue has been found. There was a prior report on bug bounty platform HackerOne, which Bitwarden was tracking following RedTeam Pentesting’s disclosure. This vulnerability was then tracked as CVE-2023-27706.
Thankfully, as previously noted, this vulnerability was fixed, but it shows that no password manager is quite perfect. As such, it remains a good idea to implement two-factor authentication, among other good cybersecurity measures, to remain as safe as possible. You never know when some clever pentester will nab your credentials in a fascinatingly roundabout way.


