New England Residents Affected By Third-Party Data Breach Of Power Companies
Earlier this morning, HotHardware was made aware that an email had gone out from Eversource, a residential energy provider in New England, to its customers warning of a data breach. This email highlighted that, like National Grid and other organizations, Eversource had been the victim of a third-party breach through a vendor, CLEAResult. It is noted in this email that while no social security numbers or financial information was leaked, customers’ names, addresses, contact information, and utility account and usage information may have been compromised.
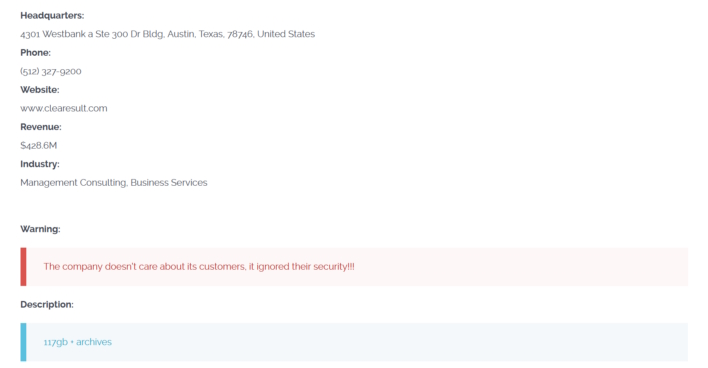
The vendor, CLEAResult, was reportedly compromised thanks to the recently discovered MOVEit vulnerabilities, the exploitation of which has affected a plethora of other businesses, such as Shutterfly, back in July. As was the case then, ransomware gang Clop has and continues to exploit the vulnerabilities, the most severe of which being CVE-2023-36934. This vulnerability is an "SQL injection vulnerability has been identified in the MOVEit Transfer web application that could allow an unauthenticated attacker to gain unauthorized access to the MOVEit Transfer database," which was discovered by Guy Lederfein of Trend Micro in collaboration with the Zero Day Initiative.
Regardless, Eversource recommends that customers monitor their accounts for unusual activity and beware of potential scam attempts. It would also be wise to change passwords for the potentially breached account and any other online account that may have used that leaked password. At this time, though, it is unclear how many people have been affected, though we are working to ascertain that information with the published breach data from Clop. In the meantime, Eversource customers or customers with any other company affiliated with CLEAResult should continue practicing good cybersecurity hygiene as details become clearer.


