Microsoft Discovers 0-Day Vulnerability Actively Exploited In SolarWinds FTP Product
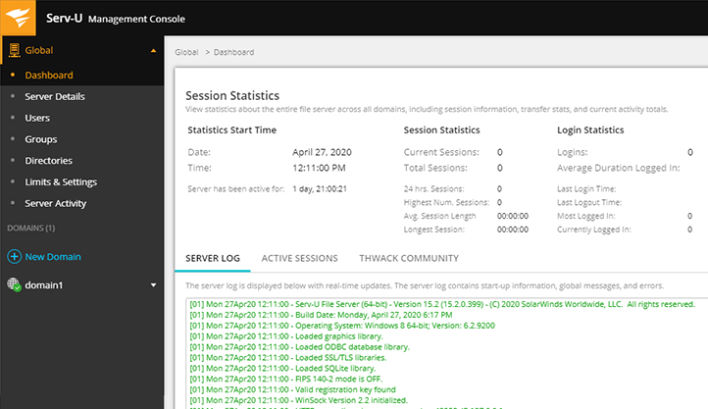
Tracked as CVE-2021-35211, the vulnerability reported to SolarWinds by Microsoft resided in Serv-U’s version of the Secure Shell (SSH) protocol, explains Microsoft’s Threat Intelligence Center (MSTIC). If Serv-U’s SSH happened to be exposed to the internet, black hat hackers could exploit the vulnerability; thus allowing for remote code execution with privileges, leading to malware installations or unwanted data access.
MSTIC further observed that the group, who used VPN solutions and compromised consumer routers among their infrastructure, targeted organizations in the U.S. Defense Industrial Base sector and software companies. Thankfully, SolarWinds responded quickly to Microsoft’s discovery and has now pushed a patch that all Serv-U customers should now download. Once again, this is a stark reminder that cybersecurity is an important investment and requires continual research.


