Google Preaches Good Cloud Security Hygiene After Calendar Gets Exploited By Hackers
The Google Q3 2023 Threat Horizons report was released, highlighting the need for cloud cybersecurity hygiene, especially with Google products. While high-profile attacks are sensational and make headlines, most breaches that organizations suffer stem from more mundane methods, such as stolen credentials allowing a threat actor to steal data stored in the cloud. Therefore, the report recommends that cloud administrators focus on simple cloud security hygiene, so as to not let anything slip through the cracks.
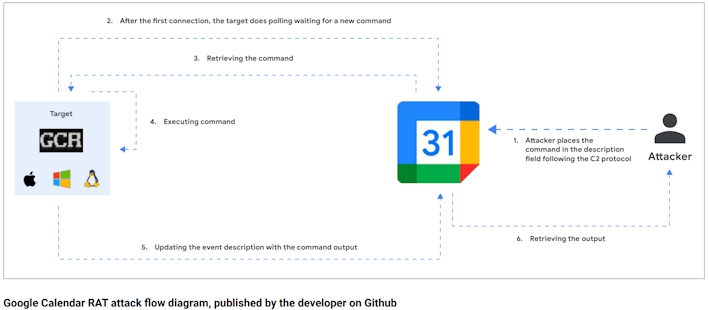
Despite best efforts, though, ithreat actors are going to continually try to outsmart and outpace defenders. The Threat Horizons report further notes that threat actors are leaning toward cloud-based services to host infrastructure. Specifically, a proof-of-concept tool called “Google Calendar RAT (GCR)” was pushed to GitHub and made the rounds in underground forums. This tool uses Google Calendar to send commands to a compromised host. While this is more like a red-teaming tool than anything, it goes to show the ingenuity of threat actors or hackers, even if they are working for a good cause.
At the end of the day, all of this serves as a reminder that anything can be leveraged against an organization given enough motivation. As such, basic security hygiene is a must to assure a baseline level of protection and to eliminate or reduce the attack surface and potential vectors of attack in general.