Framework Computer Customer Information Phished From Third-Party Vendor
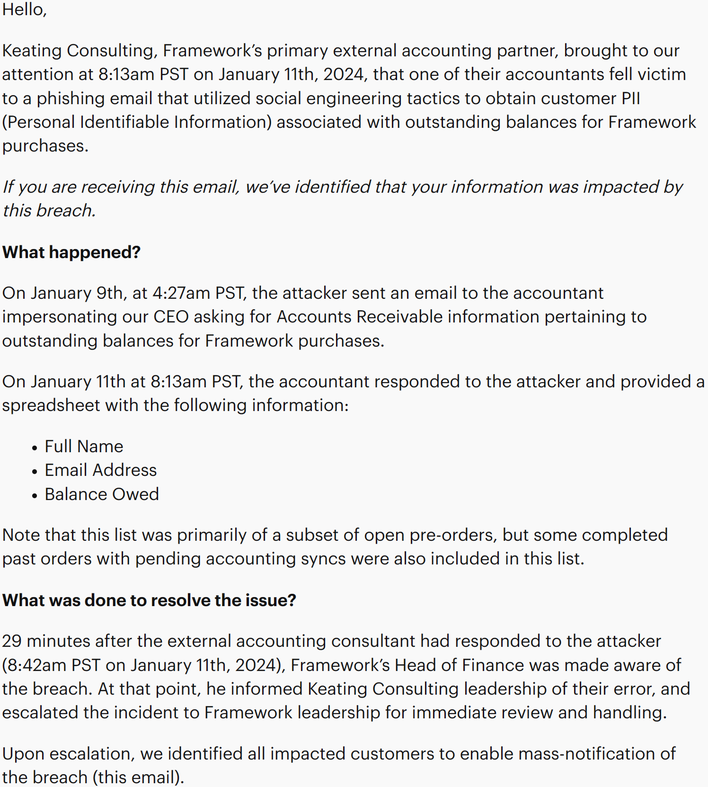
In an email that went out to affected customers, Framework explained that its primary external accounting partner reported it had fallen victim to a phishing email. This email appeared to come from Framework’s CEO asking for “Accounts Receivable” information regarding outstanding Framework orders. The accountant who got this email subsequently sent the attacker a spreadsheet containing the customers' full names, email addresses, and balances owed.
This is not a full list of customers but a subset of open-preorders as well as some completed past orders prior to accounting syncs. Regardless, 29 minutes following the attack, “Framework’s Head of Finance was made aware of the breach.” Following escalation, Framework “identified all impacted customers to enable mass-notification of the breach” with the self-referencing email. Further, Framework now requires “mandatory phishing and social engineering attack training for any [Keating Consulting] employees who have access to customer information.”
Regarding customers who had data stolen, it is recommended that they maintain a watchful eye on emails received from Framework so as not to fall victim to phishing themselves. The email explains that Framework will only send notices from the support@frame.work email and “will only provide an “Action Required” email when an official payment capture fails, which includes a link to the Framework website to update payment information to enable final payment capture.”
At the end of the day, this level of transparency and reporting should be applauded. While this is not the most severe breach we have seen, Framework's response is reassuring and impressive. Of course, it also shows that cybersecurity and phishing are serious concerns, and anyone can easily fall victim to these types of attacks.