Here’s CISA's List Of Free Cybersecurity Tools And A Security Checklist Everyone Should Know
Cyberspace is the new frontier domain of warfare, and every U.S organization is at risk as countries, and threat actors around the world wish to disrupt commerce and impact public safety. However, the barrier to entry in executing a cyberattack is lowering, and companies are becoming more complacent in their security efforts. Subsequently, CISA is publishing these tools as part of an advisory which outlines ways to protect and defend against cyberthreats by the following means:
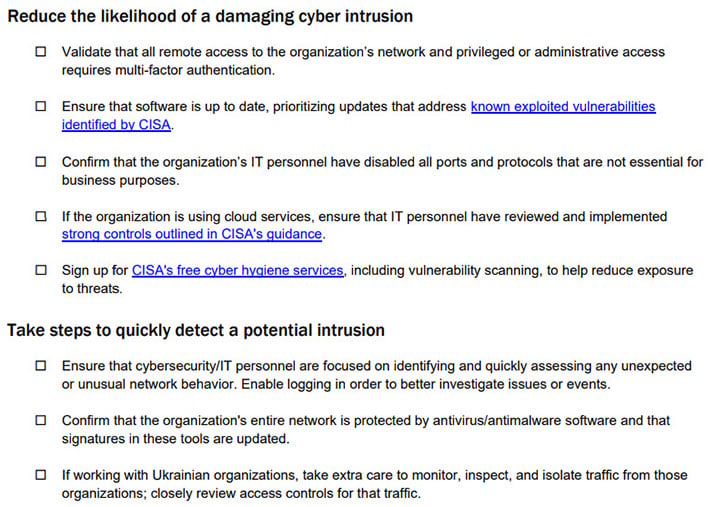
- Reducing the likelihood of a damaging cyber incident
- Detecting malicious activity quickly
- Responding effectively to confirmed incidents; and
- Maximizing resilience

As time goes on, it is expected that this list of free tools and resources will grow, as CISA describes this as a “living repository.” In any event, hopefully, this guidance and toolset will help to harden American organizations against security threats but let us know what you think of this in the comments below.


