TeamTNT Deploys Kangaroo Malware Attack On Bitcoin Targeted At Breaking Encryption
TeamTNT was a threat actor highly skilled at compromising cloud environments. The threat actor’s attacks made use of never-seen-before techniques and exploits, as TeamTNT developed its own toolbox, rather than relying on the same methods used by many other threat actors. After operating in this manner for almost two years, TeamTNT called it quits in November 2021. The threat actor subsequently ceased to develop and deploy new malware. That said, the threat actor did not take down its infrastructure, leaving its extant malware to continue its spread.
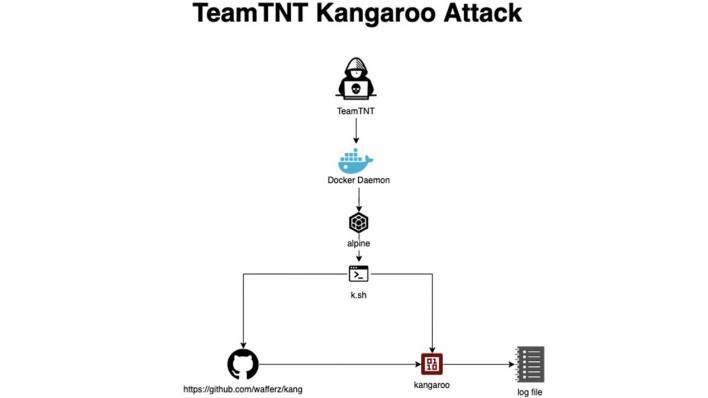
However, while the two other attacks infect victims’ systems to mine cryptocurrency, the Kangaroo attack does something of the opposite. It leverages infected environments to run a solver algorithm intended to break the SECP256K1 encryption that underlies Bitcoin. Breaking this encryption with today’s computers is considered to be a virtually impossible task, but the Kangaroo attack is tasking compromised environments with doing so anyway. The solver algorithm splits the job up into smaller tasks, enabling TeamTNT to potentially leverage a lot of stolen computer power simultaneously by distributing different chunks to each system compromised by the attack. Even so, breaking Bitcoin’s encryption in this way is still highly unlikely, making this particular attack seem somewhat strange. It's not clear what the motive or intention is behind this particular attack.

