Russia's Sinister LitterDrifter Malware That Spies On Ukraine Worms Into The US
Gamaredon, alternatively known as Primitive Bear, ACTINIUM, and Shuckworm is a Russian-backed threat group comprising of personnel from the Russian Federal Security Service (FSB). This group is primarily oriented to run large-scale espionage campaigns against Ukraine and Ukrainian entities, though they are not limited there. As of late, the group has been tied to a new USB propagating worm, which has been dubbed by researchers at Check Point LitterDrifter.
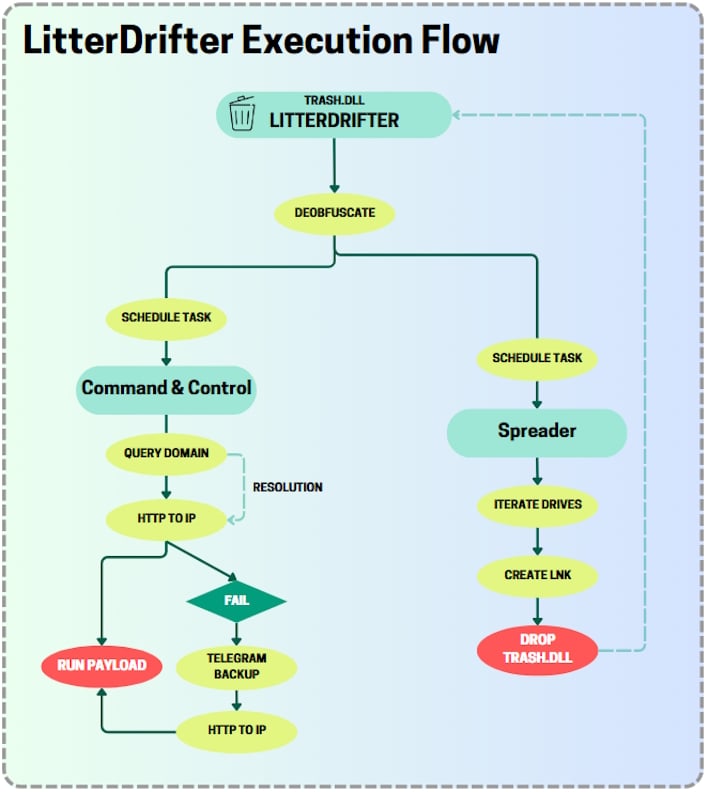
LitterDrifter is a worm written in Visual Basic Script (VBS) which has two main functions, spread over USB drives, and communicate with a vast command-and-control (C2) network. Per the Check Point report, this C2 network is rather broad and flexible, with features that “are implemented in a manner that aligns with the group’s goals, effectively maintaining a persistent command and control (C2) channel across a wide array of targets.”
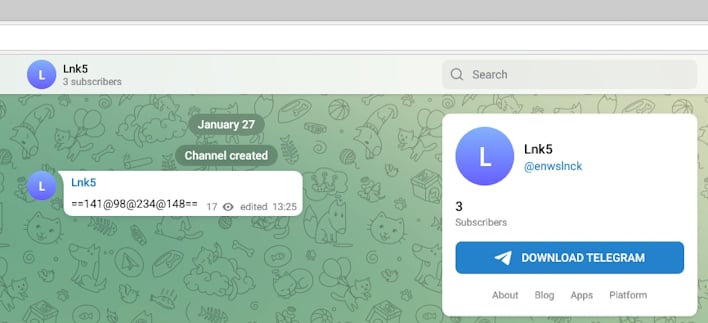
Diving into the more technical pieces of this worm, the malware has an “orchestration component” to accomplish the two main functions, all of which are contained within TRASH.DLL. This “DLL,” which is actually a VBS, establishes persistence and communications, the latter of which is actually quite interesting. The researchers explain that the C2 communication function has a fail counter that allows the worm to change how it communicates with the C2 network or get a new C2 server entirely.
While it is explained that the malware is “relatively unsophisticated” and uses simple, effective techniques, evidently, “it was designed to support a large-scale collection operation.” This is likely part of a broader cybersecurity campaign in Ukraine with the ongoing war, and there are potentially other campaigns just like this. However, with LitterDrifter’s discovery, the game of whack-a-bear played with Russian intelligence agencies continues.


