QNAP Devices Held Hostage By Ransomware Gang Using 7Zip Archives
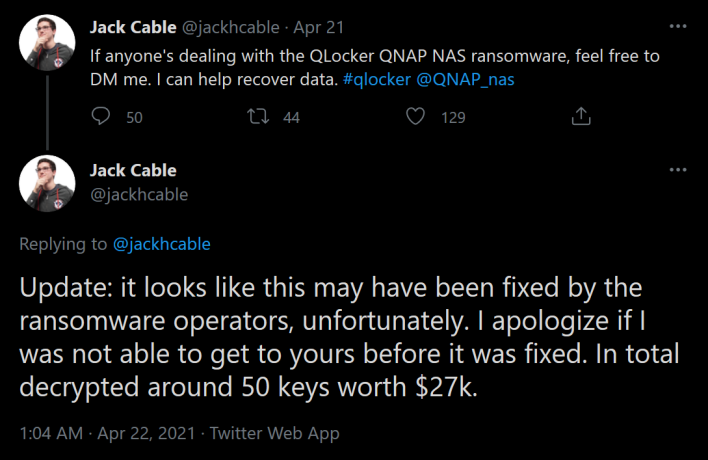
On Monday, a ransomware operation called Qlocker kicked off, exploiting new vulnerabilities in QNAP NAS devices and leaving users to wake up to their files being locked up. The ransomware gang behind this pulled it off by scanning the web for connected QNAP devices and then locking up files using the 7zip archive utility.
Command: cd /usr/local/sbin; printf '#!/bin/sh \necho $@\necho $@>>/mnt/HDA_ROOT/7z.log\nsleep 60000' > 7z.sh; chmod +x 7z.sh; mv 7z 7z.bak; mv 7z.sh 7z;
After running the command, look in the /mnt/HDA_ROOT/7z.log for a line such as the one above to show the password. Alternatively, if a user ran the QNAP Malware remover tool, the 7z.log will now be found at “/share/CACHEDEV1_DATA/.qpkg/MalwareRemover/7z.log.” QNAP is also reaching out to customers to provide help and instructions to recover a password from the log file.Example: a -mx = 0 -sdel -pmFyBIvp55M46kSxxxxxYv4EIhx7rlTD [FOLDER PATH]
Whether or not you can recover your files for free, the stress of having files held hostage is immense. To prevent this in the future, users need to make sure their devices do not face the internet as it is always a security risk. If it is absolutely necessary to be internet-facing, though, hard passwords and keeping up-to-date on patches will be essential. In any case, let us know if you were affected by the ransomware and if you managed to recover your files in the comments below.


