Microsoft Warns A Sinister Crypto Mining Botnet Is Actively Enslaving Windows And Linux
Named Sysrv-K by security researchers on Microsoft's Security Intelligence Twitter, te vulnerabilities install botnets, which will run a crypto-coin miner on infected devices. However, the method of distribution is particularly nasty and can definitely be prolific.
What Sysrv-K will do is scan the internet for web servers or exposed web servers with security holes. Assuming it finds those holes it takes advantage of them to install itself and turn on that crypto miner, which uses massive amounts of system resources. Not particularly great for anyone on a pay-as-you-go cloud system.
We encountered a new variant of the Sysrv botnet, known for exploiting vulnerabilities in web apps and databases to install coin miners on both Windows and Linux systems. The new variant, which we call Sysrv-K, sports additional exploits and can gain control of web servers.
— Microsoft Security Intelligence (@MsftSecIntel) May 13, 2022
Additionally the Sysrv-K can attempt to connect itself to other servers and devices on the network and through its scans outside of the network. That effectively also makes this an outright virus by base definition (any software that duplicates itself). That means there's a possibility of network infection, and datacenter infection.
Some of what the exploits on the Wordpress side do is related to plugins that might use certain utilities if not kept up to date properly. On the other side of vulnerabilities this takes advantage of spring cloud gateway versions prior to 3.1.1+ and 3.0.7+ as described in CVE-2022-22947.
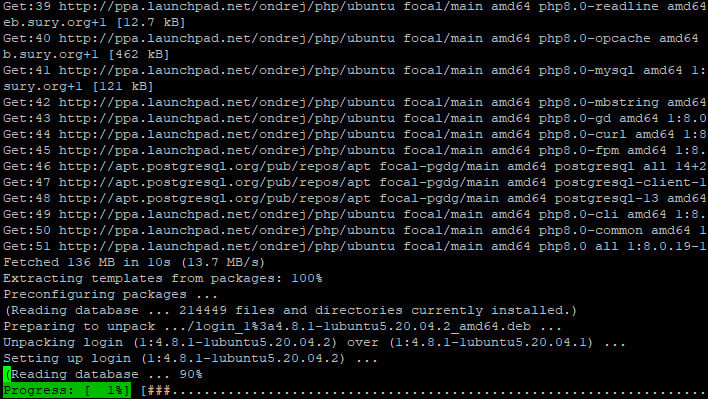
Linux Command Line apt Update

