It's that time again, time for the listing of apps that you might have downloaded that contain
malware or methods in which to plant malware on your phone. Specifically for those who utilize
Android and the Google Play Store these apps flew under the radar just long enough to wreak havoc on at least 300,000 devices. We sure hope your device isn't one, but we'll have the list of apps for you below.
These apps most commonly contain malware that is part of the Joker family. This family of malware includes methods of stealing SMS messages, contact lists, and device information. Sometimes it goes as far as signing people for premium wireless application protocol (WAP) services, these are basically services that charge a fee for their usage.
 Picture Of Joker Playing Cards
Picture Of Joker Playing Cards
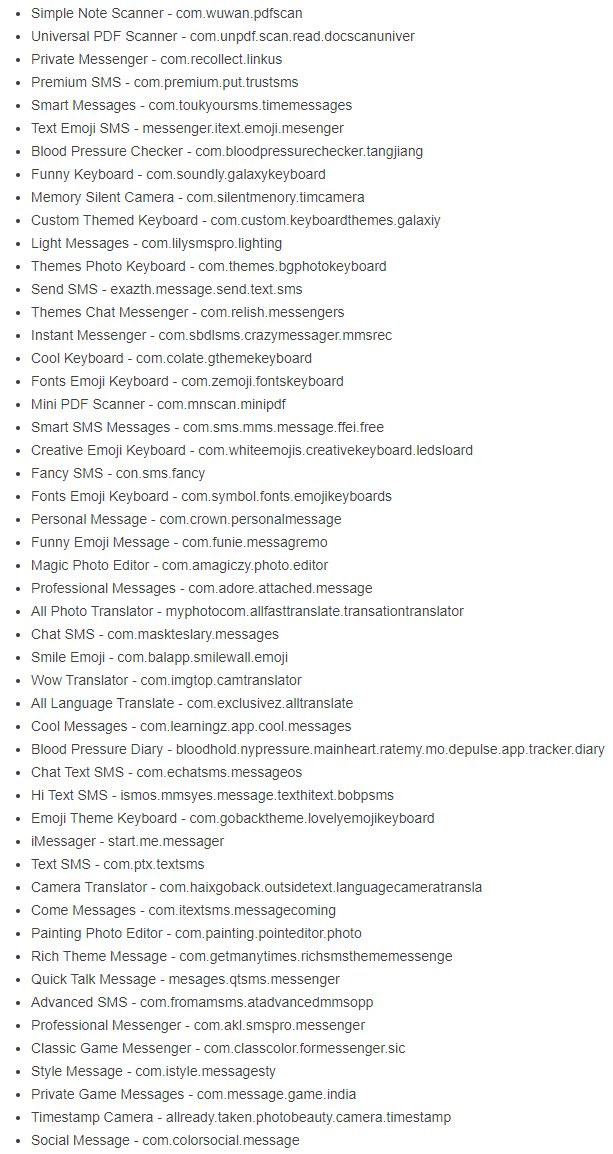
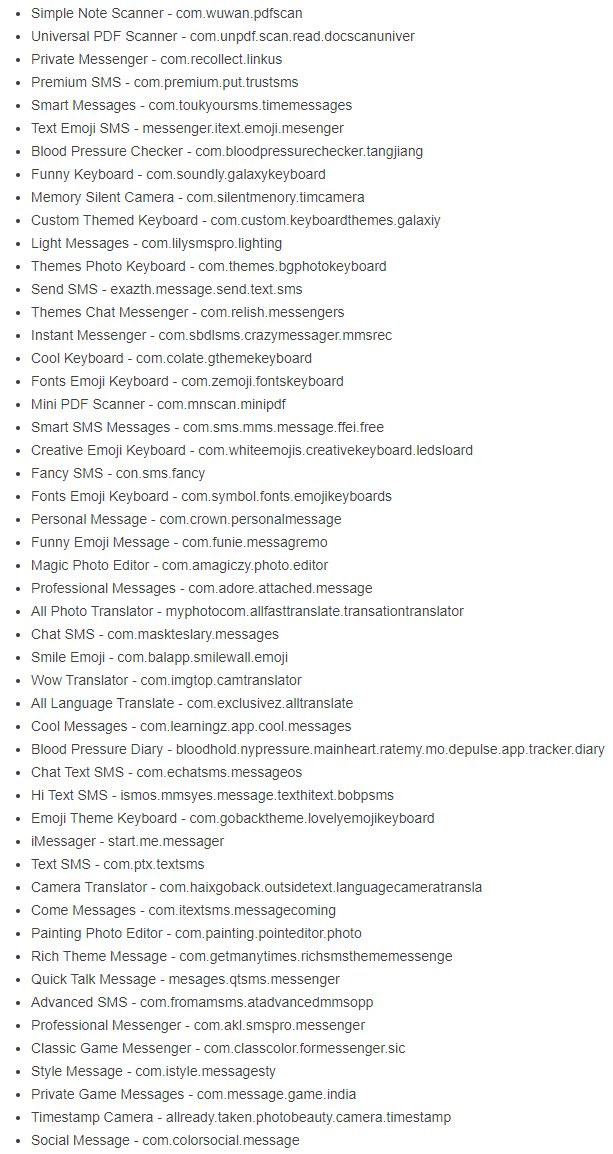
According to security research firm,
Zscaler, and their ThreatLabz, there were over 50 unique Joker downloader app on the Play Store, all under common categories of Communication, Health, Personalization, Photography, and Tools. The following is the rather extensive list of apps that include the malware downloader for Joker.
It does look like
Google has already pulled all of these from the
Play Store, however that hasn't stopped 300,00 downloads from happening anyway. If you do search through your installed apps, delete any of what you see listed above as soon as you can. Additionally you may wish to find a malware scanner for your phone, but make certain said malware scanner is actually trusted—your safest bet for this is to go through a well trusted anti-virus or anti-malware website to get an appropriate link to their mobile offering.
 Photo of Play Store App Update Setting on an Android Phone
Photo of Play Store App Update Setting on an Android Phone
What can you do to protect yourself in the future? There are a few things. First up, don't just install unnecessary, untrusted, or unvetted apps. Double check the publisher for positive review bombs, and only use apps that are recommended from sources you trust.
Additionally, don't grant notification listener permissions, or accessibility permissions to apps that you don't fully trust. Notification listener permissions are what allows those apps to view things like one-time passwords, pins, and even SMS messages. Messaging apps are a very common thing to include this kind of malware, so unless you know exactly what you're installing for a messaging app, you are better off choosing not to install one.
Also, if an app itself tells you to update and asks you to click a link or follow its instructions to update, ignore it. If there is a real update to be had you will be able to get that update from the Play Store. This linking method is a common way for malware distributors to side load malware by bypassing the Play Store. Additionally, a very common way of distributing fraudulent apps is for those malwares to take control and forward on a message with a link to people in contact lists. This is not a new method of spreading malware, but it is prevalent due to its effectiveness.
If you want to learn a bit more about the history of using contact lists to spread viruses, the
ILOVEYOU worm is a good point in malware writing history for reference.