Loapi Android Malware Packs Monero Cryptocurrency Miner That Can Fry Your Phone
Kaspersky Lab warns that the malware, Tojan.AndroidOS.Loapi or "Loapi", is targeting the Android platform. The security firm warns that Loapi can be distributed via advertisement campaigns (which can cause redirects to malicious websites that download infected packages to your device). But Loapi can also be distributed via fake/unofficial app stores and fake applications posing as the real deal. In other words, it's pretty pervasive at this point with many attack vectors.
Once on your device, Loapi will seek administration permissions, beating helpless users into submission until they eventually agree. Considering that the prompt loops until the uses gives in, it's likely that some users will acquiesce just to get the nag screen to go away.
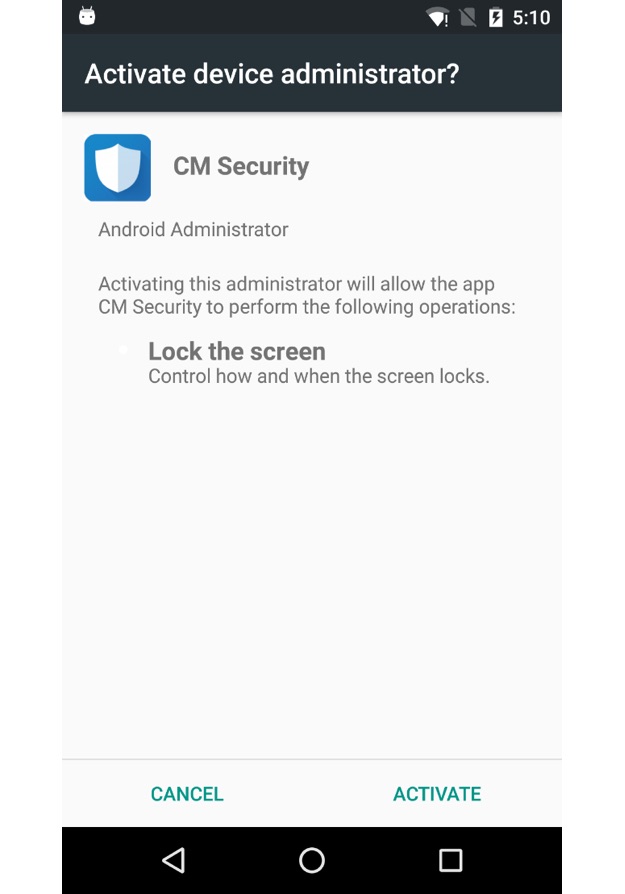
Don't fall for this scam...
There are a number of other aspects of Loapi that are disconcerting, including the fact that "self-preservation" is high on its priority list. "Loapi aggressively fights any attempts to revoke device manager permissions," writes Kaspersky. "If the user tries to take away these permissions, the malicious app locks the screen and closes the window with device manager settings.
"The Trojan is capable of receiving from its C&C server a list of apps that pose a danger. This list is used to monitor the installation and launch of those dangerous apps. If one of the apps is installed or launched, then the Trojan shows a fake message claiming it has detected some malware and, of course, prompts the user to delete it."
Sneaky, sneaky, sneaky! If that wasn't enough, Loapi has an advertisement component that will bombard your device with ads (including banner ads and video ads) that generate revenue for the author, and also includes the ability to hijack your SMS messages.

Kaspersky Lab's test device was destroyed because of the Monero mining module. (Image Source: Kaspersky Lab)
But perhaps the most dastardly module found in Loapi is its ability mine for the Monero (XMR) cryptocurrency. While a smartphone's relatively low-powered ARM processor isn't exactly the ideal platform for cryptocurrency mining, every little bit helps. However, pegging a smartphone's CPU at 100% 24-7-365 for mining purposes isn't exactly a great idea. As Kaspersky researchers discovered, their test smartphone, which was compromised by Loapi, destroyed itself after two days due to the cryptocurrency mining module. The smartphone's overtasked battery bulged due to heat and deformed the device’s chassis.
Kaspersky says that never before has it seen such malware that is truly a "jack of all trades". Given its current arsenal of weapons at this early stage in its development, there's no telling what new modules could be plugged into sharpen its fangs. Loapi could be truly weaponized, which could lead to smartphone destruction -- literally -- on a global scale.


