Western Digital MyCloud And MyBook Users Slammed By New Alarming 0-Day Security Flaw
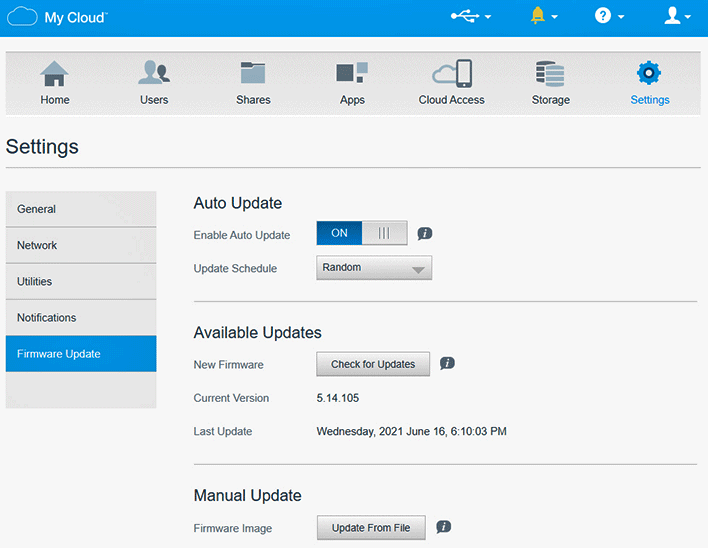
Before we go any farther, it's worth noting that WD has solved the issue with MyCloud OS 5. Owners of MyCloud devices should ensure immediately that their drives are fully updated to the latest, which is just good security practice anyhow. The company doesn't say whether the security issue was addressed in MyCloud OS 3, the previous version (there was no MyCloud OS 4, apparently), only that it stopped supporting the older OS in March of 2021. Western Digital has published a list of devices supported by MyCloud OS 5, so users can hit that to ensure they're covered.

Since WD had apparently ignored their warning, Domanski and Rebeiro intended to enter the Pwn2Own Tokyo 2020 competition with their exploit. However, just a week before the event, WD released MyCloud OS 5 complete with fixes for the security holes they had discovered. In a statement to Krebs on Security, Western Digital said:
The communication that came our way confirmed the research team involved planned to release details of the vulnerability and asked us to contact them with any questions. We didn’t have any questions so we didn’t respond. Since then, we have updated our process and respond to every report in order to avoid any miscommunication like this again. We take reports from the security research community very seriously and conduct investigations as soon as we receive them.
Because WD seemingly has not fixed this in its older firmware, the security researchers have released their own patch that will fix the configuration within MyCloud OS 3. This shell script re-launches the httpd service at startup, and needs to be re-run each time the device is rebooted. Users running devices stuck on the older firmware may want to head over to GitHub and check it out.


