105 Million Android Users Hit By Massive Dark Herring Subscription Scamware Campaign
A new Android scamware scheme may have cost unsuspecting smartphone owners hundreds of millions of dollars. Dubbed “Dark Herring” by Google App Defense Alliance member Zimperium zLabs, it’s been spotted in 470 different applications on the Google Play Store since it first showed up in March 2020.
The fraudulent apps, installed by some 105 million users in 70 countries, subscribes its victims to fraudulent premium services. A prior scamware campaign, Grifthorse, affected around 10 million Android devices worldwide. Dark Herring’s subscriptions cost $15 a month, and the scamware doesn’t even need your credit or debit card to work its dark magic.
Instead, the malware charges victims using Direct Carrier Billing (DCB), a mobile payment option that lets customers purchase content on the Google Play Store and charge it against their prepaid balance or postpaid bill.
Dark Herring used antivirus anti-detection capabilities, inclusion in hundreds of apps, code obfuscation, and the use of proxies as first-stage URLs to bilk unwitting Android users out of hundreds of millions of US dollars.
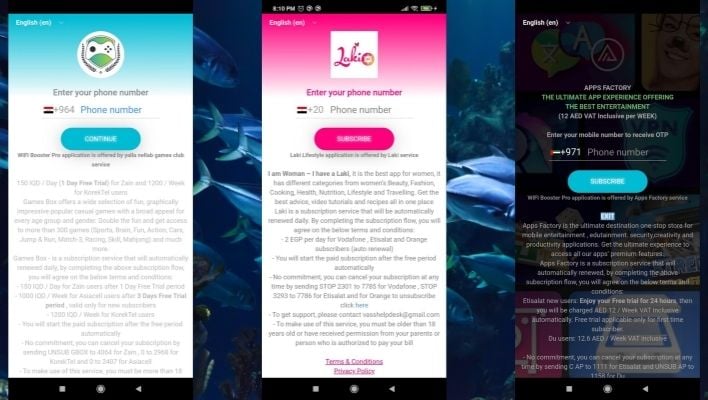
To draw in victims, the campaign served targeted malicious web pages. These pages used geolocation of users’ IP addresses to display in their local language, and asked them to submit their mobile phone number for verification. In reality, though, the page was submitting the phone numbers to a Direct Carrier Billing service to kick off a $15 per month subscription.
With this kind of scam, the user doesn’t even realize they’re a victim right away. Since nothing shows up on their credit card or bank statement, the bill could continue for months unnoticed. DCB arrangements offer little to no recourse for getting your money back, unfortunately.
Zimperium zLabs says Dark Herring is “the longest-running mobile SMS scam” it’s ever discovered. The apps involved in the scheme aren’t on Google Play anymore, but are still a threat. Several third-party app repositories still host the nefarious software.

