Remember Those Strong Password Rules? Forget Them, Here's The Real Deal
Do you need a password manager to keep track of all your obscure, special character-filled and lengthy passwords necessary for various websites? It used to be that we would pick a simple, single password for multiple accounts and websites, until the rise of online exploits and hackers made such basic security practices seem ill-conceived.
However, the recommendations of one man in particular, Bill Burr, led to the current situation that we’re in now where everything from our online banking accounts to our work email accounts require us to use a “strong” password. These are nearly impossible to remember without writing it down somewhere or filing it off into a app like LastPass (and even that isn’t bulletproof). In what could be a prime case of “too little, too late”, Burr now says that he’s sorry for putting us all through password hell.
“Much of what I did I now regret,” said Burr in an interview with The Wall Street Journal. “In the end, [the list of guidelines] was probably too complicated for a lot of folks to understand very well, and the truth is, it was barking up the wrong tree.”
Burr’s original guidelines were published nearly 15 years ago, when he worked at the National Institute of Standards and Technology. His 8-page document, “NIST Special Publication 800-63. Appendix A” [PDF], and implored computer users to use special characters mixed in with letters and numbers. Password generators can create customized and secure passwords that are harder to crack, but who has the time (or mental capacity) to remember a 16-character string of what seems like gibberish?
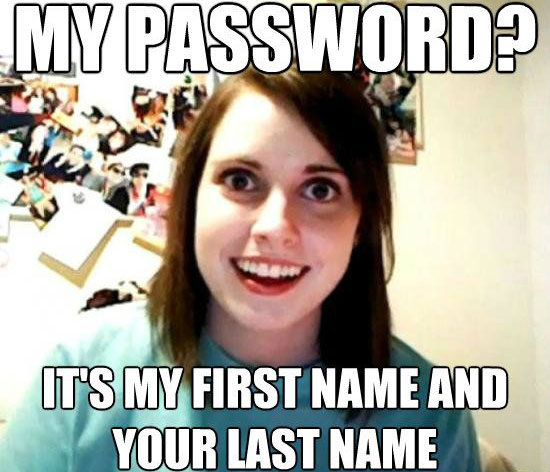
As a result, that would then prompt us to instead use passwords like “P@ssw0rd or “0DoyleRulz”. Such substitutions like replacing “o” with “0” or “a” with “@“ might seem like a good way to enhance security, but that couldn’t be farther from the truth. Hackers are quite adept at latching on to such substitutions, making them easier to crack. And Burr’s suggestion that users change their passwords every 90 days only emboldened our inherent laziness by just adding numbers to existing passwords. So “SpockerShocker” would simply transform into “SpockerShocker1”.
New guidelines put in place by the NIST changes things up (for the better it seems). Instead of changing your password every three months, it’s now suggested that you only change your password if there has been some kind of security breach that would necessitate such a change. Also, rather than using phrases with random special characters tossed in, it’s recommended that you use long phrases instead. These are likely to be easier for you to remember, but harder for nefarious individuals to decipher.
You can read the new draft guidelines from the NIST here.


