Scammers Pickpocketed $500K From Crypto Wallets By Dropping Phish Hooks In Google Ads
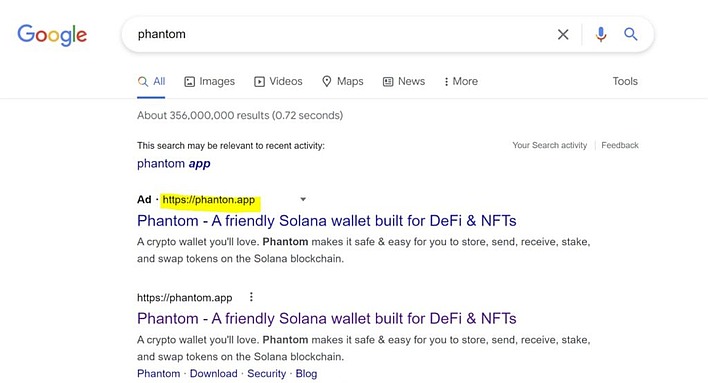
Check Point Research (CPR) has documented a new tactic in the endless war against cyber-criminals: buying Google ads. Crypto wallet users looking for popular apps like Phantom App and MetaMask have been targeted by cyber-criminals purchasing Google ads that link to their fake websites, and they look like very much like the real thing. Users that log into the fake site hand their credentials over to the thieves on a silver platter.
The security group goes on to say that these new phishing campaigns utilizing Google ads aren't the work of one actor, but of numerous agents or groups that compete with each other. They aren't just targeting Phantom and MetaMask, either; CPR points out that other popular crypto apps like PancakeSwap, UniSwap, and SushiSwap have been targeted, too.
Still, aside from the attack vector (Google ads), these phishing scams are pretty standard, so you can protect yourself with the usual methods of defending against phishing scams: always check the exact spelling of the URL, always make sure your connection is secure, and use bookmarks or shortcuts whenever you can to avoid typographical errors (or fraudulent advertisements).


