Hackers Steal $500K In Ethereum From Enigma Catalyst Platform Using Phishing Scam
If there's one thing that's been made abundantly clear over the past couple of years, it's that if you dabble in cryptocurrency, you really need to do your homework and due diligence to make sure you don't wind up on the opposite end of an attack, or scam. Some Ethereum owners are learning this lesson the hard way this week.
Enigma is a service that allows people to invest in cryptocurrency-related projects with cryptocurrency, which clearly lures in many hoping to maximize their money. Well, it also lures those who'd like a piece of that money, and are willing to get it through any means necessary. As it turns out, the means isn't too difficult.
What ultimately happened here is that certain services Enigma relies on were compromised, including Slack chat, and even its own email service. Thanks to this, attackers were able to send communication to Enigma's customers through official means. Falling for a phishing attack is pretty rare when there are so many different things that could give it away, such as the email address, but in this case, the communication appeared official.
As soon as an issue was detected, Enigma sent out pleas to its customers to not move funds around, and ensured all that wallets are safe. This is purely the result of someone gaining access to communications accounts, and wasn't a database breach.
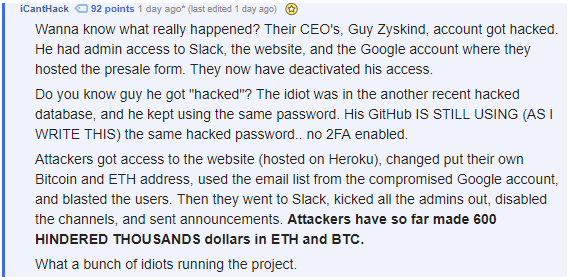
What's pretty alarming, though, is what user iCantHack said over at reddit: "Do you know guy he got "hacked"? The idiot was in the another recent hacked database, and he kept using the same password. His GitHub IS STILL USING (AS I WRITE THIS) the same hacked password.. no 2FA enabled.", something a fellow editor was able to confirm, as one of the passwords was still active."
Considering the fact that at least $500,000 in ETH has been compromised, all for what seems like awful password protection, this cryptocurrency heist could have easily been avoided.

