The Walls Are Cracking: New Report Alleges FBI, NSA Demand Passwords, Security Data When Spying On Users
A new report (albeit from unnamed industry sources, not Edward Snowden) alleges that the government has used the broad powers granted it by the Patriot Act to demand broad information about a user's passwords, website security, and even encryption information from service providers. The benefits of having this type of information are enormous, as it theoretically allows the government to directly monitor an account as email is sent and received. Email is typically the central repository for website login data and username/password information at any number of sites; it's used as identity verification when resetting mobile passwords or as part of the security process when accessing a secured site from an unknown location.
In short, having access to this information is a huge deal -- and if these allegations are true, the government has no qualms about demanding it. Again, Google, Yahoo, and other companies have trotted out representatives to claim they push back hard against these sorts of demands, and again, all the evidence suggests their pushing back is irrelevant. FISA warrants can't be challenged in court, which means the practical results of such a challenge are as follows:
FBI/NSA: "We want this information."
Yahoo, etc: "Get a warrant."
FBI/NSA: "Here you go."
Yahoo, etc: "Here's your data."
The CNET article that originally explores this topic, unfortunately, departs into left field at this point, implying that because websites liked LinkedIn and Twitter use a difficult hashing algorithm called bcrypt, it would be extremely expensive for the NSA to brute-force these passwords. The current estimate for the cost of brute-forcing a 10-character password in a single day is about $60 million dollars -- not the $1.2 billion originally estimated in 2009.
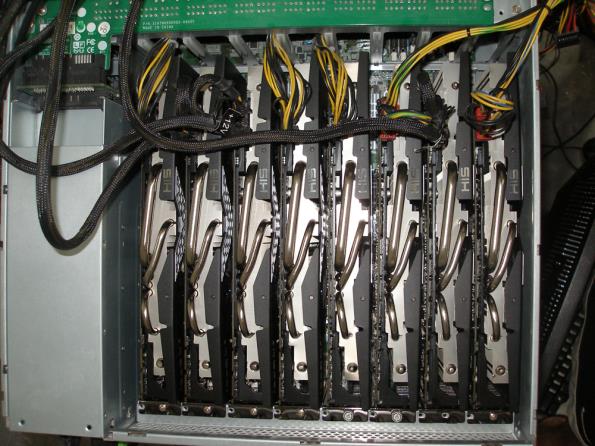
Original image courtesy of Ars Technica
Not only is it well within the NSA's capability to build a $60 million dollar computer dedicated to password cracking, empirical evidence shows it's not necessary. When LinkedIn password hashes leaked earlier this year, upwards of 100 million of them had been cracked in days. Not by brute-force -- that's the stupid, difficult, work of last resort. Instead, hackers used sophisticated hybrid attack methods that blend dictionary approaches and password-cracking rules with "try everything and see what works" algorithms. Combine that with off-the-shelf GPU hardware, and the reality is that very few passwords would take anything like that much cash to crack.
It's not that this situation fundamentally changes what we knew about the NSA's powers, it just further illustrates how completely the government's spying has infiltrated American life. The first attempt to defund the NSA's operations failed this week, but it failed narrowly; impetus for a fundamental overhaul of how the NSA does business is still growing in Congress. With multiple requests to the government for more disclosures still pending, it's encouraging to see information like this leaking out -- it's the only way to chip apart the culture of secrecy that's ossified in the 12 years since 9/11.
In short, having access to this information is a huge deal -- and if these allegations are true, the government has no qualms about demanding it. Again, Google, Yahoo, and other companies have trotted out representatives to claim they push back hard against these sorts of demands, and again, all the evidence suggests their pushing back is irrelevant. FISA warrants can't be challenged in court, which means the practical results of such a challenge are as follows:
FBI/NSA: "We want this information."
Yahoo, etc: "Get a warrant."
FBI/NSA: "Here you go."
Yahoo, etc: "Here's your data."
The CNET article that originally explores this topic, unfortunately, departs into left field at this point, implying that because websites liked LinkedIn and Twitter use a difficult hashing algorithm called bcrypt, it would be extremely expensive for the NSA to brute-force these passwords. The current estimate for the cost of brute-forcing a 10-character password in a single day is about $60 million dollars -- not the $1.2 billion originally estimated in 2009.
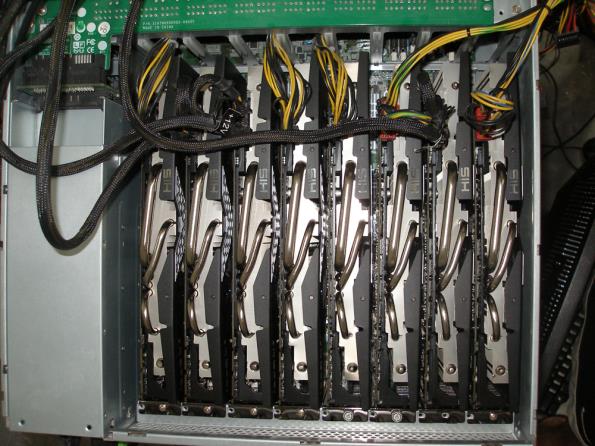
Original image courtesy of Ars Technica
Not only is it well within the NSA's capability to build a $60 million dollar computer dedicated to password cracking, empirical evidence shows it's not necessary. When LinkedIn password hashes leaked earlier this year, upwards of 100 million of them had been cracked in days. Not by brute-force -- that's the stupid, difficult, work of last resort. Instead, hackers used sophisticated hybrid attack methods that blend dictionary approaches and password-cracking rules with "try everything and see what works" algorithms. Combine that with off-the-shelf GPU hardware, and the reality is that very few passwords would take anything like that much cash to crack.
It's not that this situation fundamentally changes what we knew about the NSA's powers, it just further illustrates how completely the government's spying has infiltrated American life. The first attempt to defund the NSA's operations failed this week, but it failed narrowly; impetus for a fundamental overhaul of how the NSA does business is still growing in Congress. With multiple requests to the government for more disclosures still pending, it's encouraging to see information like this leaking out -- it's the only way to chip apart the culture of secrecy that's ossified in the 12 years since 9/11.

